Mobile Security Assessment Case Study
About Our Client
The client is one of the largest financial service providers and they offer comprehensive suite of financial products and their business includes Retail, Corporate and International Banking services, Insurance, Mutual Funds, Mortgage services and other financial services.
Objective
The client sought Varutra for advice on securing their Mobile Applications from security threats which can lead to loss of Confidentiality, Integrity and Availability (CIA) of the data. Client wanted to ensure that their Mobile Applications meet all the security standards.
The Challenge
Our Client’s business requirement was to provide mobility to all their customers for all finances. To fulfil the same, Android & iOS applications were developed to provide mobility to the customers via cross-platform support.
Major concern was to secure the customer’s sensitive data, client being from financial background has developed applications considering all secure configurations like SSL Pinning and root detection implemented.
Security Standards Followed at Varutra
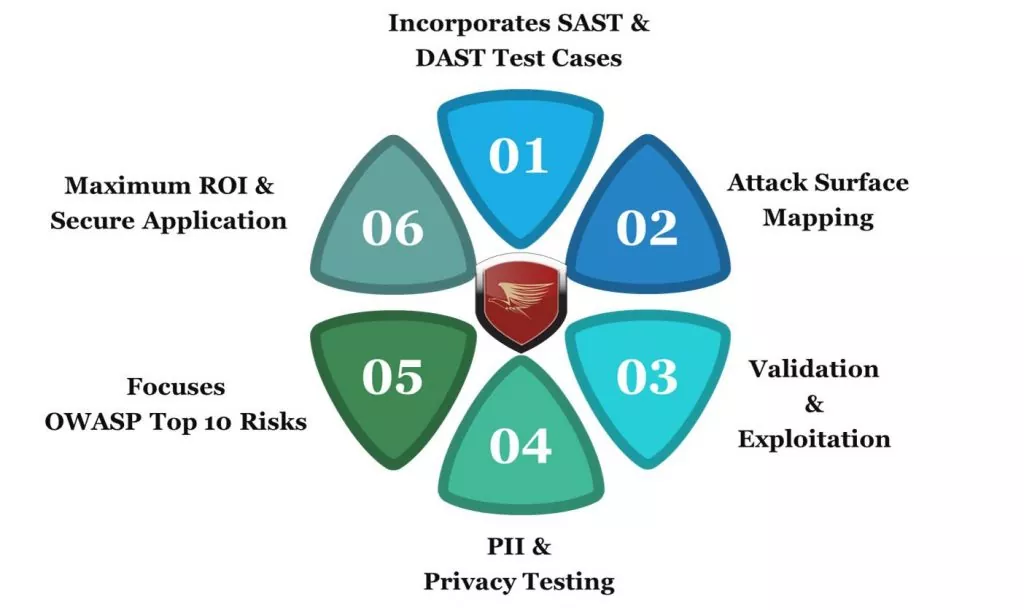
Varutra’s security assessment methodology is in accordance with best standards and follows guidelines from OSSTMM, OSINT, NIST, ISSAF, CIS and OWASP for web and mobile and SANS for Network Penetration Testing. Varutra follows Application Security Verification Standard (ASVS) which helps developers with the requirement for secure development.
Key Findings & Observations
Varutra, with its skilled Pentesters, was able to break into the mobile application by finding multiple Critical vulnerabilities such as,
- SSL Pinning Bypass
- Improper Export of Android Application Components
- Authentication Bypass
- Sensitive data in local storage and logs
- Application allows runtime debugging
- SQL Injection
- Cross-Site Scripting (XSS)
- Improper Session Management
The complete assessment was done with the automated testing using commercial and open source tools as well as extensive manual testing for verification and validation. This was the most important phase of a penetration test because it effectively demonstrates the impact of breach for the concern organization. Main targets in this phase were sensitive information revealed by the mobile application which includes sensitive API Keys, Hard coded credentials, Credit card details transmitted via logs.
Deliverables
The reports and remediation provided by Varutra were customized to match the Client’s operational environment and requirement.
The following reports were submitted to the client:
How Varutra Helped
Our Penetration Test helped numerous clients to identify the potential threats / vulnerabilities that could have compromised entire infrastructure. All of our clients are assisted in assessing percentage of potential business and operational impacts of successful attacks / exploitation. Additionally, the client gained the following benefits:
Conclusion
Penetration testing is often done for varying reasons. Two of the key goals we and our client aimed for, were to increase upper management awareness of security issues and to test intrusion detection and response capabilities. After conducting the Pentest and compromising the organization & engaged the client in a controlled offensive/defensive threat detection challenge, allowing the client several days to identify and remediate active threats within their systems.
Post completion of the assessment, Varutra was appointed to conduct training for the key internal security team like secure code development as well as further advisory on remediation tactics. In the end our client was able to meet the highest level of compliance and regulation standards, develop better security practices and reassure their customers, employees, and board of their continued dedication to best business practices and continued growth.
After mitigating all security risks by following all remediations suggested by Varutra, the client mobile application was secure from all possible risks uncovered by Varutra and effectiveness of these vulnerabilities can be verified by conducting Reassessment activity on same target mobile applications to analyze strength and the security posture.