Network Security Assessment Case Study
About Our Client
Our Client is a holding banking company and offers a range of banking services covering commercial and investment banking on the wholesale side and transactional/branch banking on the retail side. The Retail Banking segment serves retail customers through a branch network and other delivery channels, as well as through alternative delivery channels. The Bank provides its corporate and institutional clients a range of commercial and transactional banking products.
Objective
The client sought Varutra for advice on securing their entire Network Infrastructure from security threats which can lead to loss in Confidentiality, Integrity and Availability (CIA) of the data. Client wanted to ensure that their Infrastructure meets all the security standards and regulations.
The Challenge
Client’s major business goal was to provide their customers with secure platform to manage their banking transactions. Client Network infrastructure was guarded by a Firewall which was restricting all transmitted frames. Hence, Varutra had to bypass the perimeter firewall to evaluate the target scope before starting Network Security Assessment.
Security Standards Followed at Varutra
Varutra’s security assessment methodology is in accordance with best standards and follows guidelines from OSSTMM, OSINT, NIST, ISSAF, CIS and OWASP for web and mobile and SANS for Network Penetration Testing. Varutra follows Application Security Verification Standard (ASVS) which helps developers with the requirement for secure development.
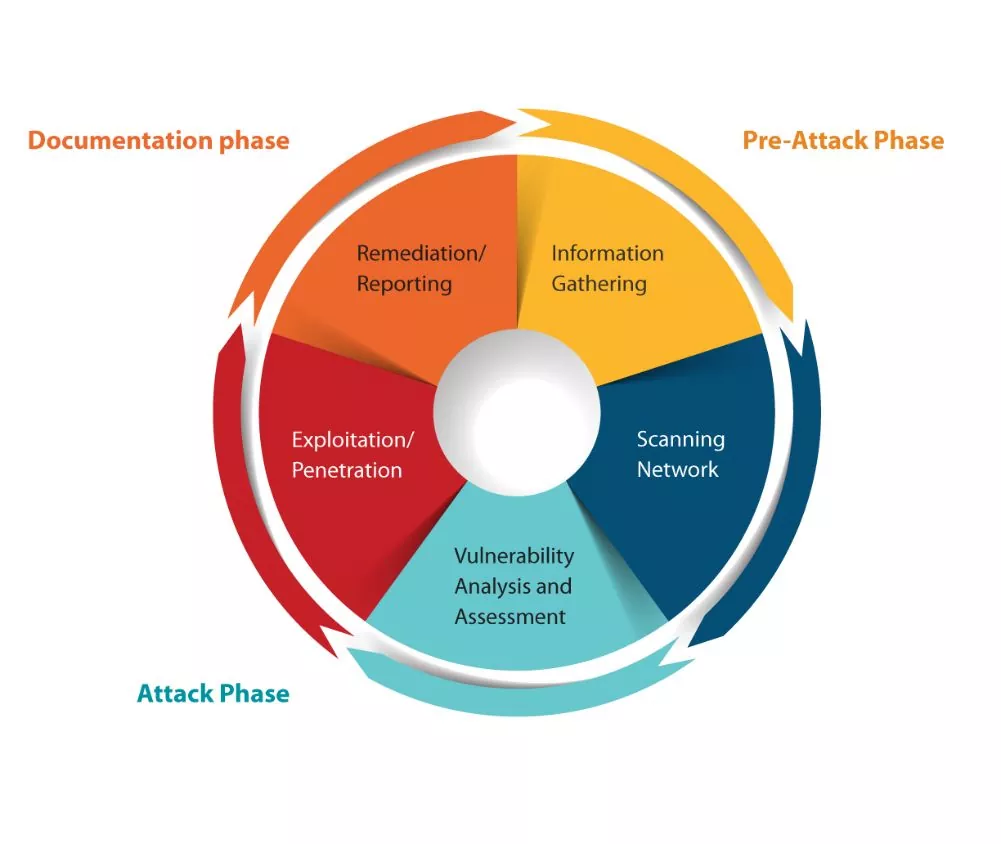
Our Approach
Varutra’s methodology involves assessing the security posture of the critical servers and networking devices to find out vulnerabilities to check the security of server systems from an attacker’s point of view; specifically, as an internet malicious user, and determine if the hosts could be compromised to gain access impacting Confidentiality, Integrity and Availability of data.
- Pentesters gathered complete information related to the organization in the Reconnaissance Phase which includes Intelligence Gathering like IP addresses, dumped data on darknet, email IDs, phone numbers which was used to perform various social engineering attacks.
- Upon performing all passive scans and gaining sensitive information related to the organization Pentesters initiated with Active scanning phase on the target which involved the scanning of various ports and find vulnerabilities related to it.
- The client network consisted of various technologies such as firewall, IPS, web servers, databases, networking devices, SMTP servers etc. The goal was to understand the current level of external risks which may compromise the sensitive data of the customer as well as the organization.
- Upon performing all passive scans and gaining sensitive information related to the organization Pentesters initiated with Active scanning phase on the target which involved the scanning of various ports and find services related to it.
- Upon identifying all open ports and services running on the target servers/networking devices Pentesters enumerated the services for more information to rectify the vulnerable services running on the target.
- After identifying the vulnerabilities in the Network infrastructure and having a brief discussion with client team, Varutra was permitted to perform exploitation of the discovered vulnerabilities which lead to Pentesters to compromise critical data servers, access to SMTP servers (Open Mail Relay protocol), and verify SMB WannaCry Vulnerability.
Key Findings & Observations
Varutra, with its skilled Pentesters, was able to break into the organization’s infrastructure using network level attack surface and gain access to the systems. While doing assessment Varutra found multiple critical vulnerabilities which are as below:
- Remote access to Critical database servers
- Eternal Blue (SMB WannaCry)
- Open mail relay on SMTP server
- Multiple servers and devices with weak credentials susceptible to brute force attacks
- Security misconfiguration on networking devices
- Encryption key or subkey were not unique per device
- No recovery / master key for database
- Misconfigured firewall solution
- Multiple medium and low severity vulnerabilities
The assessment was performed with automated testing using commercial and open source tools as well as extensive manual testing for verification and validation. This was the most important phase of a penetration test because it effectively demonstrates the impact of breach for the concerned organization.
Deliverables
The reports and remediation provided by Varutra were customized to match the Client’s operational environment and requirement.
The following reports were submitted to the client:
How Varutra Helped
Our Penetration Test helped numerous clients to identify the potential threats / vulnerabilities that could have compromised entire infrastructure. All of our clients are assisted in assessing percentage of potential business and operational impacts of successful attacks / exploitation. Additionally, the client gained the following benefits:
Conclusion
Penetration testing is often done for varying reasons. Two of the key goals our team and client aimed for, were to increase upper management awareness of security issues and to test intrusion detection and response capabilities. After conducting the Pentest and compromising the organization, we engaged the client in a controlled offensive / defensive threat detection challenge, allowing the client several days to identify and remediate active threats within their systems.
Post this challenge, the organization was assigned to conduct training for the key internal security team like secure code development as well as further advisory on remediation tactics. In the end the client was able to meet the highest level of compliance and regulation standards, develop better security practices and reassure their customers, employees, and board of their continued dedication to best business practices and continued growth.
After mitigating all security risks by following all remediations suggested by Varutra, the client infrastructure was secure from all possible risks uncovered during the assessment and effectiveness of these vulnerabilities can be verified by conducting Reassessment activity on same target scope to compare strength of the security posture.