Challenges Faced in IoT Security
What is IoT?
IoT Internet of thing is a network of the devices, things, sensors which are interconnected with each other over the internet. Today most organizations embrace the Internet of Things. By recent stats, about 75 Billion IoT devices are estimated to be in use by 2025. By the end of 2019, the global market for IoT was said to be valued at almost $1.7 trillion so IoT security is important to keep it secure.

Internet of Things
IoT Security
The increased risk in these fields can be directly related to device limitations, and because of missed opportunities to improve the security.
In the last few years, the hacking of internet devices and websites has increased tremendously. Given the current situation of work from home due to the crisis worldwide, hacking has seen a spike as confirmed by many resources. By the survey to Gartner, at least one IoT attack is observed by 20% of organizations in the last 3 years.
The IoT Hacks
The following are some examples of recent IoT attacks over the globe.
- MIRAI Botnet Attacks Oct 2016
- The SUV Jeep Hack by IBM 2015
- St. Jude medical Cardiac Device Hack 2017
- Hackable Connected printers in the USA
Moreover, as technology is growing rapidly, the use of IoT has seen a boost. In the situations, if the network of systems is controlled by an IOT device and if the device itself gets attacked then the whole network gets affected automatically, which can be dangerous as they may be breach huge amounts of data.
In this blog, we will talk about a portion of the fundamental challenges for IoT security.
Irregular Update Mechanisms and Default Settings
One of the important things that are necessary today is the regular update of our systems. A properly updated network or system is less vulnerable to attacks than a system that is rarely updated or updated once or twice a year.
The IoT device manufacturers show a lack of interest in providing regular firmware updates. It may lead to compromise the IoT device/network at a large scale
Similarly, Numerous IoT devices come with built-in default settings or lack of ability to make systems more secure by restricting operators by modifying configurations. The OWASP top 10 for IoT highlighted this in its one of the top 10 IoT vulnerabilities.
Considering the example of the router, the Router is the fundamental passage to the system and all devices associated with it. Along these lines, somebody who has acquired your Router key could change the settings and capture the system, leaving you without getting to it.
Here are some default passwords of popular routers
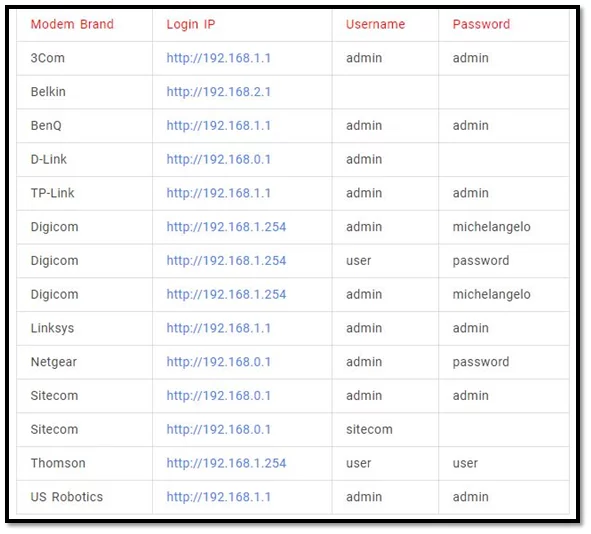
Source:- TechMania
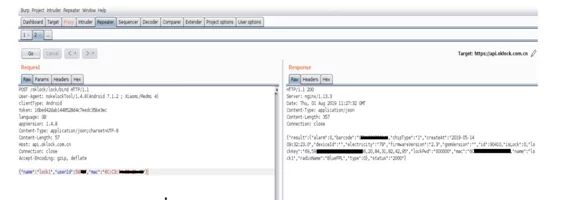
Insufficient Encryption
As encryption is a way to prevent hackers from accessing data, it is also one of the leading IoT security challenges. IoT gadgets must be inbuilt with their solid security and encryption principles. Current Internet security conventions depend on a notable and generally confided set-up of cryptography Algorithms. For example, the AES for Confidentiality, RSA for Digital signature and key transport, SHAS1, and SHAS256 for secure hash algorithms. This set-up of calculations is enhanced by a lot of developing awry calculations, known as Elliptic Curve. This suite was designed with the expectations of resources like device storage and capacities. Most IoT devices lack storage and processing capabilities. The result is an increase in attacks where hackers can easily manipulate the algorithms that were designed for protection. Unless an enterprise resolves this issue, encryption won’t be a security asset.
The following Image shows the plaintext credentials from the unencrypted MQTT protocol.
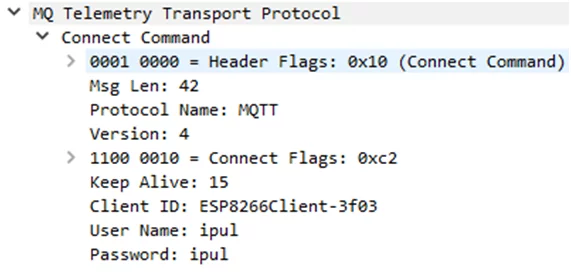
Source: – ResearchGate
Lack of Security Awareness
The education and awareness about security threats among the vendors, manufacturers, and especially end-users are vital. The purchasers who purchase IoT devices are ignorant of the security issues regarding the item. A basic consumer is just mindful of fundamental usefulness like, how to utilize the gadget for a particular reason.
For example, the user who is more enthusiastic about new smart devices always buys a new updated smart product for their home or industry application, but they are not aware of the safety or data security operations of that product.

Source: https://www.king5.com/article/news/local/baby-monitor-hack/281-0f06509a-42bd-4108-b884-718c79e55e0f#:~:text=SEATTLE%20%E2%80%94%20A%20Seattle%20family%20is,year%2Dold%20calling%20from%20upstairs.
Rising Malware and Ransomware attacks
The rapid rise in the development of IoT products will make cyberattack permutations unpredictable. Cybercriminals have become advanced today — and they lock out the consumers from using their devices. For example, an IoT-enabled camera that captures confidential information from home or the work office — and the system is hacked. The attackers will encrypt the webcam system and not allow consumers to access any information. Since the system contains personal data, they can ask consumers to pay a hefty amount to recover their data. When this occurs, it’s called ransomware.
- Here are some types of malware attack
- MITM
- Malware through advertisement i.e., Malvertising
- Drive-by-downloads
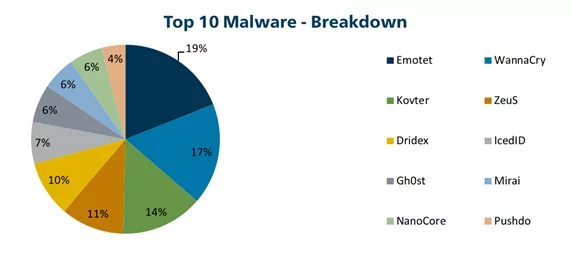
Source: -cisecurity
Lack of Authorization and Authentication
With such huge numbers of Smart Devices offering potential purposes of passage inside an IoT framework, basic authentication and authorization should be a must for making secure IoT systems. Each node or device must set up its unique identity before it can get to entryways and upstream administrations and applications. Most of the devices get tumbled down during authentication when the system implements weak essential secret key confirmation or passwords inalterable methods.
Most of the So-called “Smart lock” gets compromised with its security. The attacker was able to take over the account of respective victims and unlock the lock via its mobile application
Read more about FB 50 Smart lock Hack
Intricate IoT Ecosystem
In the 21st century enterprises have numerous methods to detect a hack or manipulate devices using various security protocols. However, due to the huge increase in IoT devices the threat detection method used could be less reliable and hence making the whole process challenging. Complex IoT systems are and will be the problem.
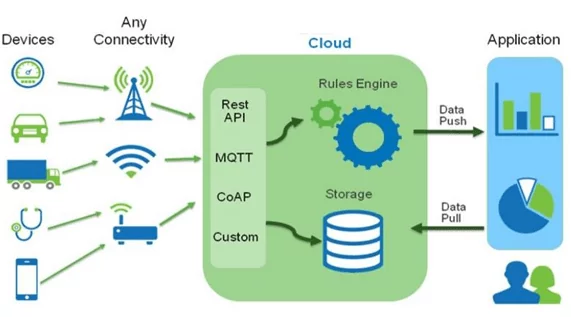
At this point when we talk about IoT gadgets, they incorporate
- Hardware chip-sets.
- Storage and Processing capacity.
- Network Connectivity
- Internal communication protocols like UART, SPI, I2C, etc.
- API’s
- The main operating systems i.e., firmware.
- Cloud storage
- Transport mechanisms
- Organizing radio communication like Wi-Fi, BLE, MQTT, Zigbee, LORA, and so forth.
- Mobile and web application.
This makes the individual gadget and their system exceptionally complex to delve into each security perspective identified with the gadgets and correspondences. From a security viewpoint, sadly, we neglect to make sure about all aspects of these perplexing frameworks.
Conclusion:
In this blog, we discussed some present security challenges for the internet of things. As the network of IoT devices increasing rapidly, in coming years these challenges will be the toughest task for the IoT device manufacturers as well as IoT infrastructure providers. The manufacturers must apply strict IoT security policies throughout the development cycle of the IoT product/ infrastructure.
References:
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13143
- https://www.csoonline.com/article/3258748/the-mirai-botnet-explained-how-teen-scammers-and-cctv-cameras-almost-brought-down-the-internet.html
- https://www.peerbits.com/blog/biggest-iot-security-challenges.html
- https://www.netsparker.com/blog/web-security/the-challenges-of-ensuring-iot-security/
Author,
Shubham Chougule
Attack & Pentest Team
Varutra Consulting Pvt. Ltd.