What to Expect When You’ve Been Hit with Ransomware?
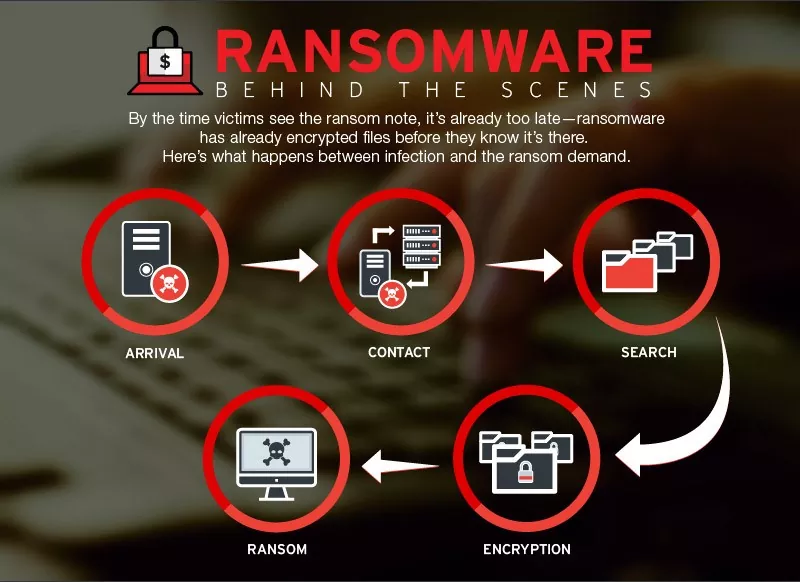
Ransomware is malicious software or malware that gains access to the system, denies you any admission to your network, system, or files, and demands payment…
Ransomware Trends: Higher Ransom Demands, More Extortion Tactics
Ransomware attacks have been a severe issue for the past couple of years and are evolving daily. Organizations widely incorporate advanced cybersecurity technologies and improvised…
3 Must-Haves in Your Cybersecurity Incident Response Plan
Cyber-attacks never issue any prior intimation or warning; it just happens anytime. Basically, with cybersecurity incidents, it is a matter of “when” rather than “if.”…
Planning Your Cybersecurity Budget For 2022
Cyber threats and risks are a topic of global concern now. Everyone is looking for the best solutions to protect themselves against these arising cybersecurity…
Ransomware and the measures to safeguard an organisation
Ransomware Attack and Its Prevention We are all aware of ransomware, as most of us, or at least someone in our connection might be a…
Challenges Faced in IoT Security
What is IoT? IoT Internet of thing is a network of the devices, things, sensors which are interconnected with each other over the internet. Today…
Security Advisory – Ransomware Attack Targeting China – December 2018
Ransomware Attack Targeting China – Security Advisory 1. Ransomware through Supply Chain Attack: A new ransomware strain spreading as a result of supply chain attack…
Threat Advisory Report on Petya Ransomware (Critical Severity)
Threat Advisory Report on Petya Ransomware Attack (Critical Severity) Ransomware: An Introduction Ransomware is a form of malicious software that locks up users files on…
Beware Android Users – CLOAK AND DAGGER is here to exploit you
The WORLD has still not got over with the WannaCry ransomware menace and here comes one more android ransomware – Cloak and Dagger! People have…
Threat Advisory Report on WannaCry Ransomware (Critical Severity)
Here we will discuss Threat Advisory Report on WannaCry Ransomware (Critical Severity). 1. Introduction On Friday, May 12, countless organizations around the world began fending…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)