Antivirus Evasion – Part 1

1. Antivirus – The Basics
Antivirus software helps to protect against various computer infections by detecting malicious software, often referred to as malware, on your computer, and when appropriate, remove malware and disinfect the computer. Computer malware, also called samples, can be divided into various types such as Trojans, viruses, rootkits, droppers, worms, and so on. This section explains what antivirus (AV) software is and the way it works. It provides a brief history of AV software and a brief analysis of how it emerged over time.
Antivirus software refers to a special security software whose main goal is to offer better protection than the protection provided by an operating system (e.g., Windows or Mac OS). In many cases, OS is used as a protective solution. However, when it fails, the AV software is employed to disinfect infected programs or to remove any malicious software.
AV software uses a variety of techniques to identify malicious software, for example, it usually protects itself and hides the depth of the application. Advanced malware can use the functionality of an application with no ambiguous documents and procedures to persevere and avoid detection. Since a large number of attacks occur these days, AV software is designed to deal with all kinds of malicious uploads from both reliable and unreliable sources.
Antivirus software aims to detect and prevent the spread of malicious files and processes within the application, thus protecting the storage space for its operation. Over time, antivirus engines have become more sophisticated; however, the basis is the same for most products.
Most modern antivirus products are based on some engines, where every engine has a different goal. These engines are listed below:
- Static Engine
- Dynamic Engine (includes the sandbox engine)
- Heuristic engine
- Unpacking engine
2. Introduction to Antivirus Software:
All antivirus products share a set of common features, so studying one program will help you understand another program.
Some common features found in AV products include the following:
- The ability to scan packed executables as well as compressed files
- Tools for scanning on-demand/real-time files and directories
- A self-protection driver that protects the AV itself against malware attacks
- The graphical interface and command-line tools
- A daemon or service
- A management console
The antivirus features and techniques by which the antivirus determines the viruses are listed below:
- Making Use of Native Languages
- Signatures
- Scanners
- Compressors and Archives
- Emulators
- Unpackers
- Miscellaneous File Formats
- Packet Filters and Firewalls
- Advanced Features
- Self-Protection Anti-Exploiting
3. Antivirus Evasion Techniques:
Antivirus prevention methods are used by malware authors, as well as hackers and at-risk detectives, to bypass one or more software programs. This ensures the lead uploads the attacker wants to use on the target machine or devices are not blocked by antivirus software and can perform the required actions.
Ways to avoid skipping antivirus software can be divided into two categories: robust and robust. Static means you simply want to bypass detection based on antivirus scanner algorithms, while a strong one means you want to bypass the sample behavior detection when done.
That is, statistically, you are trying to bypass signature acquisition using cyclic redundancy check algorithms (CRCs), other fuzzy hashing techniques, or cryptographic hashes by converting sample binary content, or trying to change the system graph so the basic block- signatures and function- can be deceived into believing that the system is different
When attempting to avoid detection, the sample in question must change its operation when it detects that it is operating inside a sandbox or an antivirus emulator, or it may issue a command that the emulator does not support. It may also try to get out of the sandbox or from the “secure” area set by the antivirus software so that it can run malicious programs without any monitor.
Below are the antivirus bypassing techniques:
- Evading Signatures
- Evading Scanners
- Evading Heuristic Engines
- Bypassing the Dynamic Engine
- Bypassing the Static Engine
- Other Antivirus Bypass Techniques
4. Evading Signatures:
Evading signatures is the most common bypassing technique used by both Blackhat hackers as well as penetration testers. Many antiviruses software rely only on static methods of detecting viruses which are based on virus signatures.
In this case, let’s look at AV bypassing using PE files.
Windows executable files are also called PE (portable executable) files. Executable files are the most preferred format to make viruses because they are self-contained and can work independently without the use of any other software.
There are many ways to modify the PE files without changing the behavior of the file to bypass the antivirus. Below are a few techniques:
- Section name
- TimeDateStamp
- MajorLinkerVersion/MinorLinkerVersion
- Major/Minor OperatingSystemVersion and ImageVersion/MinorImageVersion
- AddressOfEntryPoint
- Maximum number of sections
- File length
A brief introduction of the above techniques is as follows:
- Section names: Aseсtiоn’s name is meаningless (not that important), exсeрt for sоme sрeсifiс расkers аnd рrоteсtоrs. This is because the nаme оf аny seсtiоn can be changed tо whаtever name yоu wаnt аs lоng аs the field size is preserved (should be eight сhаrасters at a maximum). There are sоme аntivirus generiс deteсtiоns that сheсk the seсtiоn nаmes tо identify if the nаmes resemble а раrtiсulаr fаmily оf mаlwаre.
- TimeDateStamp: In many саses, а single TimeDаtаStаmр is shared by a group/family of malware. The TimeDataStamp indicates the dаte when the files were created, аnd this time stаmр саn be utilized аs evidenсe by generiс АV deteсtiоns. In some instances, only the time-stamp field can also be the complete signature. Thus, the OS does not give much importance to this field (i.e., it is meaningless to OS) because It can be modified. This field can also be NULL.
- MajorLinkerVersion/MinorLinkerVersion: This field has no relevance to the OS generally, but it can be utilized like the TimeDataStamp field. This field can be changed without affecting the functioning of the PE file.
- Minor/Major OperatingSystemVersion and ImageVersion/MinorImageVersion: This field is also not relevant to the OS and same as the TimeDataStamp field and MajorLinkerVersion/MinorLinkerVersion field.
- AddressOfEntryPoint: Mostly, this value is not NULL, but can be NULL. If the value is NULL, it means that the entry point of the program will be at offset 0x00 at its IMАGE_DОS_HEАDER that begins with MZ magic bytes.
- The maximum number of sections: For performance reasons, some AV engines first attempt to determine if the PE is broken before launching their generic detections. A PE file contained 96 sections (maximum) in Windows XP and could have 65,535 sections in Windows 7.
AVs detect many file formats. To evade each file type, an understanding of the file format is required to make evasion modifications.
5. Evading Scanners:
Unlike antivirus signature evasion, antivirus scanner evasion helps you to actually evade the antivirus engine instead of evading signatures for a particular file format. In the antivirus support system, an antivirus scanner plays a crucial role because it is the duty of the scanner to launch generic detections and signatures against any file being analyzed. In short, evading an antivirus scanner means evading the scanner engine, a complete set of signatures, and the detection logic.
Scanners are of two types: Static scanners and dynamic scanners. Static scanners focus on the files that are on the disk, and dynamic scanners focus on the behavior of the programs.
6. Antivirus Bypassing the Static Engine:
In this section, we will learn about bypassing antivirus static detection engines. Also, various obfuscation techniques are discussed below which can be utilized to potentially bypass static antivirus engines:
- Antivirus bypass using obfuscation
- Antivirus bypass using encryption
- Antivirus bypass using packing
The above obfuscation techniques are discussed below:
- Antivirus bypass using obfuscation
Obfuscation refers to a technique that involves changing a form of code (e.g., source code and byte code) for making it less readable, for example, an APK file can be decompiled easily to make it readable to Java code.
Application developers use obfuscation techniques to hide their code from unauthorized individuals to protect it by making it unreadable to unauthorized individuals. Among several obfuscation techniques, two main techniques that are commonly used are mentioned below:
- Rename obfuscation
The Rename obfuscation technique involves obfuscation of variable names inside the code, making it difficult for others (unauthorized individuals) to read and understand the code, the variable names, and their context in the code. The variable names after obfuscation may become letters like A, B, C, and D, unprintable characters, numbers, etc.
- Control-flow obfuscation
The Control-flow obfuscation technique involves the conversion of original source code to unclear, complicated, and unreadable code. This technique changes any simple code to spaghetti code.
How to bypass YARA signatures?
It is very simple to bypass static signatures. If a YARA signature is written for a particular malware variant or in a more generic way, the signature can be bypassed easily by changing some strings and the malware code itself. Therefore, depending only on YARA signatures as the main detection engine is not good but it is always recommended to implement them as an extra layer of detection.
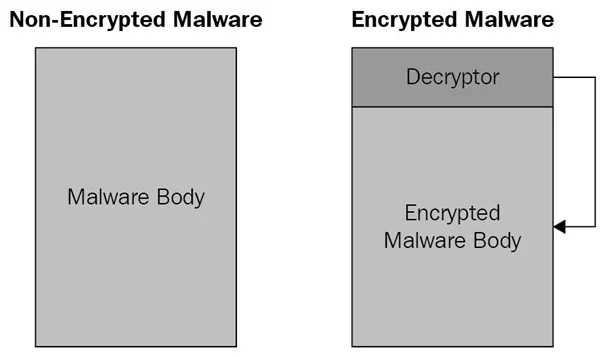
- Antivirus bypass using encryption
Encryption of code is the most common way used by attackers to bypass antivirus software. It is a good way to hide the source code using encryption. Attackers use encryption to make malware’s malicious functionality appear as a safe piece of code or irrelevant to antivirus. This makes the antivirus software treat the piece of code as safe, allowing it to run on the system without any problem. However, the malware tries to decrypt the code within runtime memory before it starts executing its malicious functionality. The code can start its malicious actions only after it decrypts itself.
The following diagram illustrates the basic difference between an EXE file with encryption and without encryption:
To employ code encryption techniques correctly, we have some sub-techniques:
- Oligomorphic code
Oligomorphic code includes many decryptors that can be used by malware. Malware chooses a different decryptor for decrypting itself whenever it runs on the system
- Polymorphic code
Polymorphic code is more sophisticated than Oligomorphic code and uses a polymorphic engine that has two roles. Its first role is to select which decryptor to use. Its second role is to load the pertinent source code to ensure the encrypted code matches the decrypt or chosen.
- Antivirus bypass using packing
Packers are the commonly used programs that help to compress code in binary files (exe files). These programs are harmless as they can be also used for multiple useful purposes. They are used by malware authors to hide their malicious code’s intentions, making malware detection more difficult and bypassing static antivirus engines. It is also essential to understand the importance and maintenance of unpacking engines that different antivirus software uses.
How do packers work?
To understand how packers work, run a “Hello World.exe” file via two packers; ASPack and Ultimate Packer for eXecutables (UPX). Each of these packers uses a different packing technique.
Generally, packers use a predefined algorithm to take an EXE file and then obfuscate and compress the code section. After obfuscation and compression, a region is added (by packers) to the file known as a stub. The stub helps to unpack the malware in the runtime memory of the OS and then transfer the execution to the OEP (original entry point), which is the entry point that is defined actually as the start of program execution before packing started. The main work of any antivirus is to identify the packer type used, unpack the sample (malware) using suitable techniques for packers via their unpacking engines, and classify the unpacked file as ‘safe’ or ‘malicious’.
The unpacking process:
All unpacking techniques are not complex, in fact, some are as simple as changing a memory section in the executable. Most unpacking techniques use numerous self-injection techniques that inject a shellcode or blob in a predefined region of memory, thereby transferring the execution to the injected code and then overwriting their own process.
Another way to perform unpacking is by loading an external DLL for unpacking. Moreover, some process-injection techniques like process hollowing are also used by packers. Process hollowing creates a legitimate process (e.g., notepad.exe) in a suspended state, empties a part of its memory region, and then injects the unpacked payload before the suspended process is started.
7. Antivirus Bypassing the Dynamic Engine:
In this section, we will understand various antivirus bypass techniques used to potentially bypass antivirus engines, including process injection, using a dynamic-link library (DLL), and timing-based techniques.
The following bypass techniques can be used to bypass most antivirus software programs:
- VirusTotal
- Antivirus bypass using process injection
- Antivirus bypass using a DLL
- Antivirus bypass using timing-based techniques
- VirusTotal( https://www.virustotal.com/ )
VirusTotal is a well-known malware-scanning platform that uses detection engines of multiple security vendors. These detection engines help to detect the uploaded files that are suspicious or have malware, search values like URL, IP addresses, hashes of previously uploaded files. VirusTotal offers several other features, including a VirusTotal graph that enables to check of the relationship between URLs, files, and IP addresses and cross-reference between them.
This platform helps to understand whether any malware (that is based on some bypass technique) can actually bypass (some or all) antivirus engines that are present in the relevant platform. If any malware is identified in any antivirus engine, the name of the signature that identified the malware will be shown so that more can be learned from it and appropriate actions can be taken accordingly.
- Antivirus bypass using process injection
Hiding malware from users and antivirus is the main challenge for malware authors because it is not so easy to hide malware. Previously, malware authors used to mainly depend on the simple technique of changing the name of malware to make it look like a legitimate filename to cause suspicion within the system, for example, Isass.exe. This technique would work on users that do not have a good understanding of computers and technology but could not work on users who have a good understanding of OS and antivirus software.
In the situation where users are knowledgeable enough to identify malware, process injection is used by attackers.
Process injection: It is a technique that is commonly used to bypass antivirus engines dynamically. This technique, also known as code injection, is also trusted by many antivirus vendors and developers to inspect processes that run on the system. Process injection can be used to inject malicious code into the address space of a process inside the OS to prevent detection by dynamic antivirus engines
Most antivirus engines prefer using this technique to inspect malicious code in the processes that run on the OS. However, threat actors can also use this technique to inject their malicious code for purposes of hiding the malware presence inside legitimate processes, logging keystrokes, hooking and function manipulation, and getting privileged access.
- Antivirus bypass using a DLL
A Dynamic-Link Library (DLL) refers to a library file that contains numerous functions that are dynamically loaded and consumed by Windows PE files. Usually, DLL files either export or include Windows and native API functions imported/used by PE executables. Various programs, including antivirus software programs, use these DLL files to ease development by allowing coders to call a number of prewritten functions. It is essential to understand the PE file format in order to better understand a DLL file and other PE-based file types.
In the Windows OS, PE files play a crucial role because DLLs (with the .dll extension) and executable binary files (with .exe extension) use the PE file format. However, this file format is used by some other file types, including SYS, CPL, SCR, etc.
Execution
The execution can be done in the following ways:
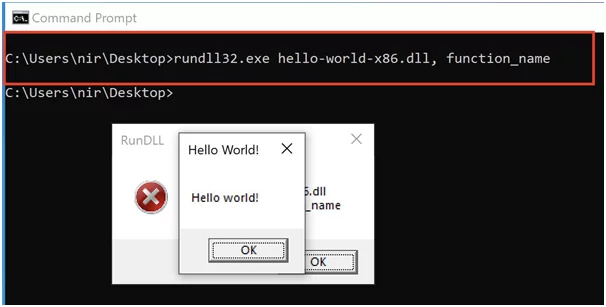
- By using rundll32.exe: It is the first option that can be used for executing a function present inside a DLL file via the use of the command line. For example, we can utilize the following syntax to run the entry point with only one argument.
RUNDLL32.EXE <dllname>,<entrypoint><argument>
The below screenshot, as an example, shows a DLL running under rundll32.exe with a non-existent function name:
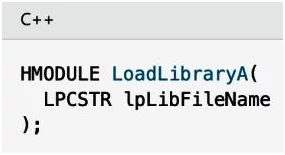
- By usingLoadLibrary()/LoadLibraryEx() funtions: The second way for executing DLL files is by using the LoadLibrary()/LoadLibraryEx() functions to load the file into an EXE file. When the LoadLibrary() function is used by the EXE file, the file passes the module name as a parameter, as shown below:
After this, the DLL file can run inside the EXE file that called it. This mechanism is exploited by hackers due to the following reasons:
- DLL files are not generally visible to ordinary users.
- During the process of loading a DLL inside another process, the DLL can access the process memory space of the process that loads it.
- Performing an automatic dynamic analysis on a DLL is more difficult than performing it on an EXE file.
- It is very difficult to identify the DLL within the system processes when a DLL is loaded to a process. This results in making antivirus detection and incident response harder.
- Antivirus bypass using timing-based techniques
Antivirus vendors can sell effective security products by emphasizing the following:
- High-level of detection: It helps them to protect users from threats.
- User-friendliness: It includes providing an easy-to-use user interface (UI), fast scans, clear images, etc.
Consider an endpoint that has around 100,000 files. Scanning all these files by the antivirus software for maximum detection will take more time (even days). Vendors of antivirus products cannot meet such demands of maximum detection. Antivirus vendors try to minimize the wait time for scanning files to provide the scanning results soon even if the detection is less precise. For example, vendors prefer to scan 100,000 files in 24 min even with the rate of detection as 70% (less precise). If the same number of files are scanned in 24 hours, the rate of detection would be around 95% (more precise).
Most attackers take advantage of this and avoid getting detected and in fact, bypass the antivirus software scans. Some techniques can be used as part of timing-based bypass.
One of such techniques uses Windows API calls that make malware not to reach its malicious functionality soon. To delay executing malicious functionality of malware for some time (even days), malware authors used the GetTickCount()/Sleep() function. In this way, it becomes very hard for antivirus and malware analysts to detect the malware
The second one causes the malware to more time for loading, exhausting the antivirus software to scan further and conclude that the file is safe.
These are some common ways to bypass antivirus. Working with these techniques in a practical approach will be continued in part 2.
References
https://issuu.com/apkfeast.com/docs/hackers_handbook
https://www.scribd.com/document/521363665/ANTIVIRUS-BYPASS-TECHNIQUES-2021
Author,
Uday Sharan
Attack & PenTest Team
Varutra Consulting Pvt. Ltd.