How Hackers Use Social Engineering to Spread Dridex Malware
What is Dridex Malware? Dridex is a highly sophisticated form of malware that has been active since 2014, with the primary goal of stealing banking…
Understanding Deep and Dark Web and Exploring Its Threats
The internet comprises millions of web pages, servers, and databases operating 24/7. But the web we use is often addressed as the “visible” internet called…
Top 10 Cybersecurity Threats
There is a significant shift in the digital landscape as people rely on the internet more and more across the globe. But unfortunately, it also…
Antivirus Evasion – Part 1
1. Antivirus – The Basics Antivirus software helps to protect against various computer infections by detecting malicious software, often referred to as malware, on your…
Adware – New Age Weapon
Are you seeing ads every time while browsing the web and it is asking you to install software or enter personal details? Clicking on links…
Open Redirect
What is Open Redirect? An open redirect is a security flaw in an application or a web page that causes URLs to fail to authenticate…
MALWARE ANALYSIS – PART 2 (SETTING UP THE LAB)
In the previous blog, we have got a basic idea about Malware like what is malware, its behavior, types, and a brief introduction to Malware…
Joanap and Brambul Malware
Joanap and Brambul Malware has come from North Korea that has infected numerous Microsoft Windows computers globally over the last decade. On 30th January 2019 United…
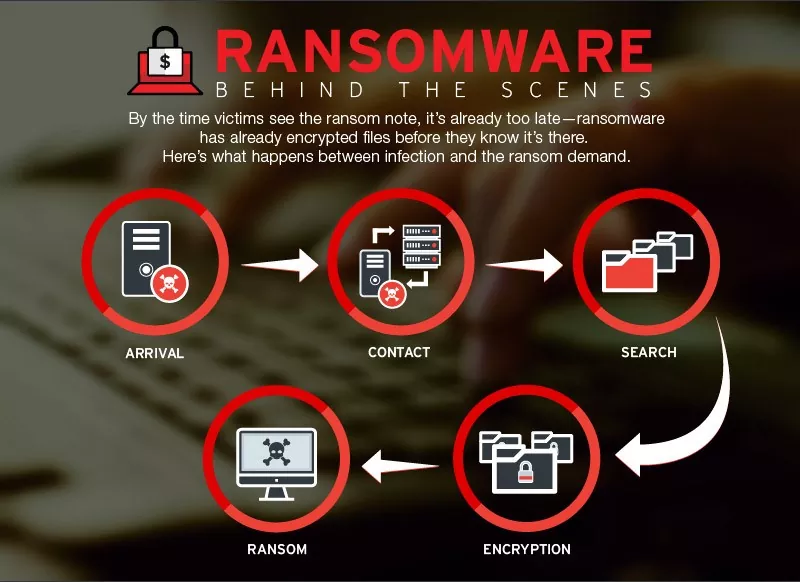
Security Advisory – Ransomware Attack Targeting China – December 2018
Ransomware Attack Targeting China – Security Advisory 1. Ransomware through Supply Chain Attack: A new ransomware strain spreading as a result of supply chain attack…
Security Advisory – Tecnimont Cyber Theft
Tecnimont Cyber Theft – Security Advisory Background: Maire Tecnimont SpA is the parent company of the Italian group Maire Tecnimont, which consists of at…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)