Deception Technology: The Art of Recording Cyber Attacks
Introduction To Deception technology:
Deception technology is a newest strategy to attract cyber criminals away from an enterprise’s true assets and divert them to a trap of decoys which imitate the real assets of the organization to safeguard the real endpoints from external attacks.
Deception technology imitates genuine assets of the real network infrastructure and is an effective approach to detect the threats proactively with less false positives and minimal performance impact on the network operations.
Importance of Deception Technology:
Honeypots were the first form of deception technology and were used in 1990s in order to deceive malicious actors into interacting with a false system. Later, honeypots would gather the attacker data and asses the malicious intent performed. It should be noted that honeypots are limited in scope and it is very easy for an attacker to identify them as the system which will either have no outbound traffic or the traffic will be fabricated and will not typically follow a normal usage pattern. Hence, experienced threat actors can figure out the honeypots very quickly and easily.
Honeypots were originally intended to allow the security analyst to observe attacks in progress, capture and retain them for further learning. They still serve an important purpose in threat research and can be used effectively for cyber-forensic analysis, threat hunting and analysis, developing responses to malicious behavior. Honeypots may still prove useful, but not as effective as modern deception technology strategy focused on threat detection.
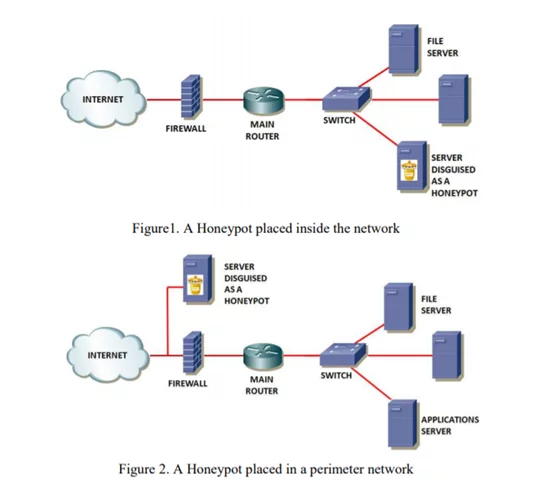
Image Source: http://proceedings.informingscience.org/InSITE2008/InSITE08p069-076Hernan422.pdf
Evolution of Deception Technology:
Honeypots are labor-intensive and is a passive line of defense, relying on attackers to somehow identify them as high-value targets. They also need to be updated, maintained on a periodic basis which makes them a tiresome solution to maintain.
Like other technologies, Honeypots also needed an evolutionary leap to cope up with the sophisticated attacks. Hence the latest Deception Technology is built on the idea of Decoys by redirecting hackers towards fake assets where the real endpoints stay protected.
Image Source: https://www.wwt.com/article/deception-technology
Benefits of Deception Technology:
The primary aim of Deception technology is to prevent a cyber-criminal that has managed to infiltrate a network from performing any malicious act. It often uses a mix of lures to trick attackers, and then refreshes or updates themselves in attracting attackers.
The technology works by generating decoys that imitate legitimate technology assets throughout the network infrastructure. The decoys can run in a virtual or real operating system environment. They are designed to trick the cyber-criminals into thinking that they have discovered an organization’s asset and has the access to escalate privileges and steal credentials.
Once a trap is triggered, alerts are sent to a centralized deception server that records the affected decoy and the attack vectors that were used by the cyber-criminal which can be further used for the analysis.
Decoys are often made to look authentic using artificial intelligence and it will have common network naming conventions and it also includes shared folders and drives to create false activity trails which mimics the actual behaviour of an endpoint.
Image Source : The rapid evolution of deception technologies, NTT Security
Deception technology provides numerous benefits when it comes to early detection of intruders, which is the key to minimize impact of future cyber-attacks. Adding decoys to an organization’s network can give the security team upper hand in terms of detection speed and grant access to valuable information needed for the analysis of the security incident.
Several benefits of implementing Deception technology also include:
- Greater coverage of assets under protection
- Gaining visibility across the network
- Improved Threat Detection
- Proactive Business Risk awareness
- Reduction in dwell time and the mean time to detect an alert and remediate
- Eliminates Alert fatigue
Deception technology can also protect an organization from Credential theft, Man-in-the-Middle attacks, Sensitive data theft, lateral movement of Malware, attacks on Directory systems (container that is used to contain folders and files), Geo-fencing etc.
Use Cases:
- Using Deception Technology against the Cyber Kill Chain Process:
Deception will be used to detect threats across the Cyber-kill chain starting with Reconnaissance which will be followed by certain stages of attack, ultimately leading to data theft. Below image gives the idea regarding the type of decoys employed at every stage of Cyber-kill chain to safeguard the organization from data theft.
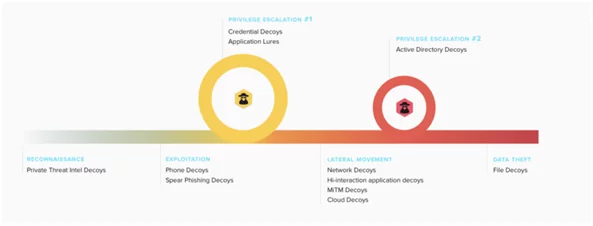
Image Source : https://www.smokescreen.io/deception-technology-101/
- Endpoint Protection with Deception:
This technology works by planting fake information throughout the environment. Whenever a decoy file is placed on User’s (endpoint) system, it is unlikely to affect any tasks user needs to perform.
But to an attacker the decoy appears to have legitimate and valuable information and is accessed by the user who can be later targeted for data exfiltration. Couple of fake processes, folders, files and similar information will be included in the decoy to make it look legitimate.
Once the attacker accesses the decoy and performs the operations, centralized deception servers will alert the security team. Further, the security team can record the patterns, record the indicators of compromise, do the analysis of ongoing attack without compromising the actual assets of the organization.
- UEBA (User Entity and Behavior Analytics) with Deception:
UEBA systems are prone to false positives due to inbuilt self-learning algorithms. In larger geographic areas, security analysts might find it difficult to validate each and every alert due to lack of context (Alice in the London security team doesn’t know why Bob is uploading a lot of data in India).
UEBA combined with Deception can provide excellent enrichment in eliminating the user backstory. For example, if a decoy file is copied and the user is suddenly logging in outside of office hours concurrently from two places, the centralized deception servers are likely to detect it and alert the SOC Team.
References:
- https://www.rapid7.com/solutions/deception-technology/
- https://www.forcepoint.com/cyber-edu/deception-technology
Author,
Poornima Jambigi
Managed SOC Team
Varutra Consulting Pvt. Ltd.


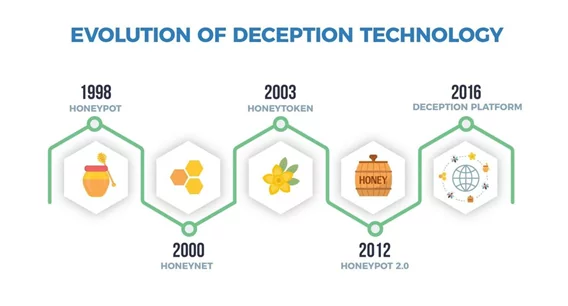 Image Source:
Image Source: 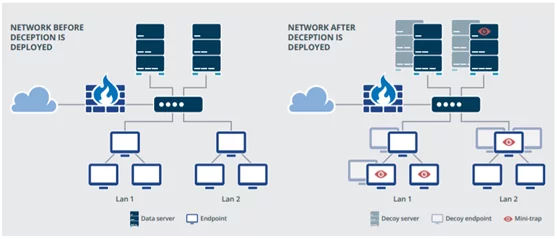 Image Source : The rapid evolution of deception technologies, NTT Security
Image Source : The rapid evolution of deception technologies, NTT Security

