Root Detection Bypass Vulnerabilities: A Crucial Aspect of Mobile App Security
Introduction
In today’s interconnected world, where smartphones are an extension of our lives, ensuring the security of mobile applications is paramount. However, this task is fraught with challenges, one of which is dealing with vulnerabilities. Rooting, the process that grants users elevated control over their Android devices, is a double-edged sword. While it offers exciting opportunities for customization and innovation, it also opens the door to potential security breaches. In response, developers employ root detection mechanisms to fortify their applications, creating a digital fortress to ward off threats.
This blog post on ‘Root Detection Bypass Vulnerabilities’ explores various aspects of vulnerabilities, shedding light on the risks, implications, and strategies for mitigation.

Rooting Android Devices: Understanding the Basics
Rooting is a procedure through which users can gain elevated control, often referred to as root access, over their devices. In the case of Android, which is built upon the Linux kernel, rooting grants users’ similar administrative privileges.
Rooted Detection Bypass: Overcoming Security Measures
One significant aspect associated with rooting is the challenge it poses to mobile application developers. To ensure the security of their applications, developers often implement android root detection mechanisms. These mechanisms are designed to prevent users with rooted devices from accessing the application. However, attempts to bypass these security measures can compromise the application’s integrity. Weakly developed android root detection mechanisms can be exploited, enabling users to gain access to the application on rooted devices. This, in turn, grants them privileged access to sensitive files, potentially introducing vulnerabilities into the system.
Bypassing Rooting Detection Methodology using Java Function Hooking
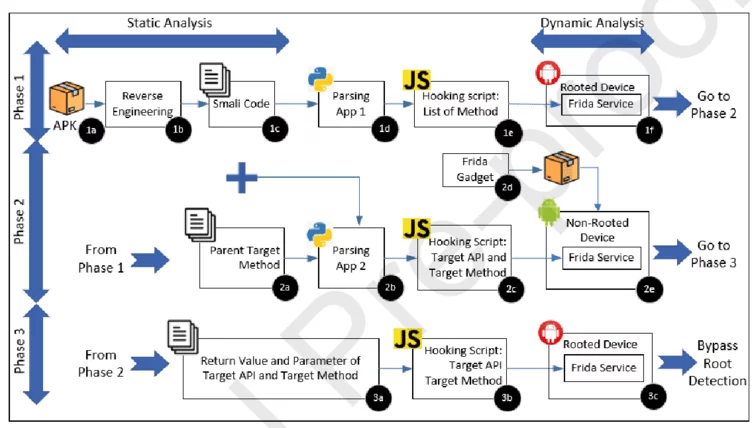
https://www.researchgate.net/figure/Bypassing-Rooting-Detection-Methodology-using-Java-Function-Hooking_fig1_343122291
Pre-Requisites: What You Need Before Getting Started
1. Rooted device or Emulator
• Rooted devices or emulators provide an environment for advanced testing and analysis, allowing researchers to explore deep system-level interactions.
• These devices are indispensable for assessing security vulnerabilities and debugging applications at a lower level.
• Emulators offer a safe and controlled environment for testing without the need for physical hardware, making them valuable for development and testing processes.
2.Platform tool or ADB
• Platform tools, such as Android Debug Bridge (ADB), serve as a crucial bridge between your computer and an Android device or emulator, enabling various commands and data transfer.
• ADB is indispensable for installing, debugging, and managing Android applications, making it an essential component of Android development.
• These tools empower developers and security researchers to execute commands, transfer files, and troubleshoot Android devices efficiently.
3.Frida-loader apk (for Frida server)
• Frida-loader APK acts as the gateway to the Frida dynamic instrumentation toolkit, allowing users to inject custom scripts into running applications.
• This APK facilitates the deployment of Frida server, making it easier to initiate dynamic analysis and manipulation of Android apps.
• Frida-loader plays a pivotal role in application security testing and reverse engineering, offering dynamic insights into app behavior and vulnerabilities.
4. Python
• Python is a versatile and widely used programming language that plays a vital role in various stages of mobile application analysis and scripting.
• Python’s extensive library support simplifies tasks like data manipulation, automation, and custom script development in the context of app security testing.
• Its cross-platform compatibility and ease of use make Python a preferred choice for many security researchers and developers in the mobile app analysis field.
5. Frida
• Frida is a powerful dynamic instrumentation toolkit that allows for real-time manipulation, monitoring, and analysis of applications on various platforms.
• Frida is a versatile tool that allows for the injection of custom scripts into running processes, providing valuable insights into app behavior, identifying security weaknesses, and pinpointing vulnerabilities.
• Frida’s flexibility and wide adoption in the security community make it an essential tool for dynamic analysis and penetration testing of mobile apps.
6. Application .apk
The .apk file format represents Android application packages, containing all the resources and code necessary for an Android app to run.
These files are the building blocks of Android apps and are used for installation and distribution via the Google Play Store or other means.
Analyzing the .apk file allows security experts to dissect an application’s code, permissions, and potential security issues before installation, aiding in security assessments and vulnerability identification.
Impact: The Consequences of SSL Pinning Bypass
• It permits users to acquire administrative access, enabling them to engage in activities that may expose vulnerabilities.
• It facilitates both static and dynamic analysis of applications.
• With administrative access, an attacker gains the ability to read, write, and access sensitive information, which can subsequently be at risk of compromise.
Steps to Reproduce: Bypassing SSL Pinning – A Step-by-Step Guide <
1. Start by launching the emulator; in this case, a Genymotion device is used, which comes rooted by default.
2. Next, download the Frida loader APK from FridaLoader – https://github.com/dineshshetty/FridaLoader/releases/tag/v3
3. After downloading the APK, place it in the ADB folder and install it on your mobile device. There are two methods to achieve this:
4.Drag and drop the APK from your system to the device.
OR
Alternatively, execute the ADB command: ” adb install APK_NAME”
5. Open the application and select “Download and Install Frida Server.” It will be automatically installed and activated on your device.
6. Now, let’s install Frida-tools on your system using the following commands:
Pip install Frida-tools
• To verify that Frida is functioning correctly and to monitor active Windows applications, you can use the following method: Frida-ps
• To identify currently active mobile applications, use the following command: Frida-ps -aiU
With all the setup and configuration steps completed, you’re now ready to proceed with bypassing root detection.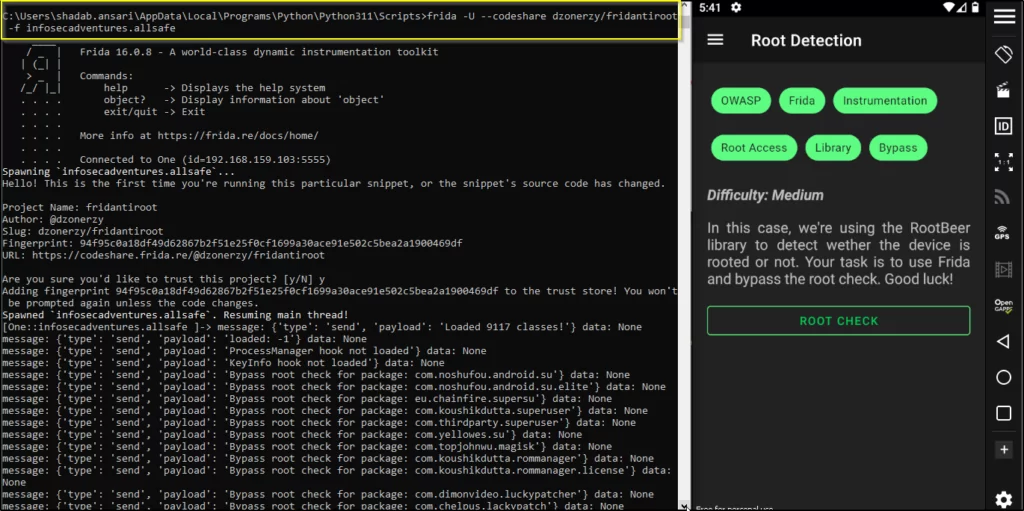
Frida for bypassing root detection
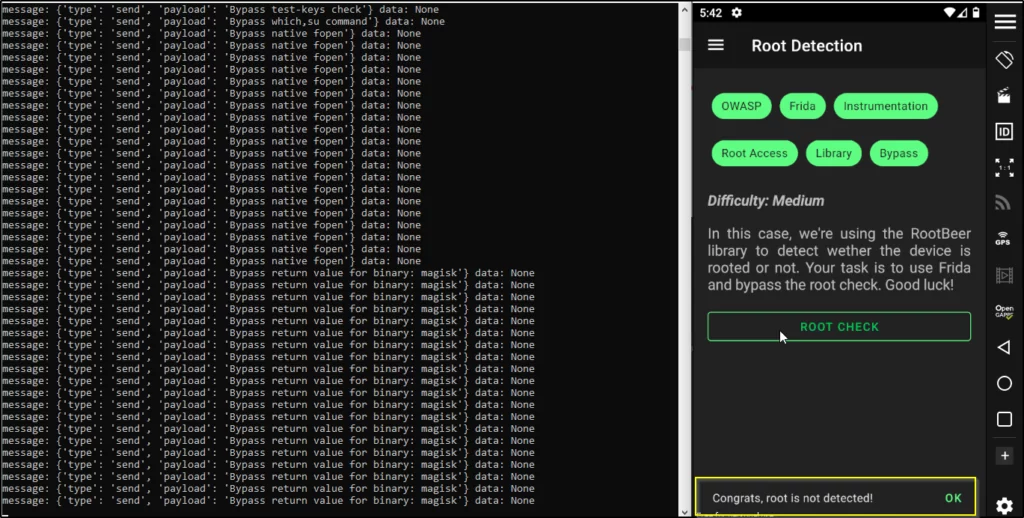
Successfully root detection bypassed
Mitigation Measures: Strengthening SSL Security
•
Implement Emulator Detection:
Implementing emulator detection means adding safeguards to spot and prevent the app from running on emulator environments typically used for testing. This ensures the app operates only on real devices, reducing the risk of unauthorized access or tampering.
•
Implement Google SafetyNet Attestation API:
By integrating Google SafetyNet Attestation API, especially its ctsProfile and basicIntegrity checks, you bolster security. These checks assess whether the device is compatible and intact, adding an extra layer of protection against potential issues on compromised or rooted devices.
•
Implement Root Detection Checks:
Root detection checks involve examining whether a device is rooted using various methods. Implementing these checks helps identify rooted devices and take necessary precautions, safeguarding your app against potential vulnerabilities and misuse.
•
Implement Frida Detect:
Frida detection mechanisms are crucial for spotting attempts to use the Frida toolkit to manipulate your app. By implementing Frida detection, you strengthen security, thwarting potential attacks that rely on this toolkit for dynamic analysis and manipulation.
•
Implement Magisk Detection:
Magisk is a common root solution among users. Implementing Magisk detection techniques helps your app recognize and respond to Magisk-rooted devices, adding an extra layer of defense against potential security breaches.
•
Code Obfuscation:
Code obfuscation involves transforming your app’s source code to make it difficult for attackers to understand or reverse-engineer. This security practice safeguards your app’s inner workings and algorithms, improving overall security by discouraging malicious attempts to decipher your code’s functionality.
Conclusion
In conclusion, the battle for mobile application security (hyperlink: https://www.varutra.com/cyber-security-services/mobile-applications-security/) rages on, with root detection serving as a stalwart guardian. However, as attackers continue to refine their tactics, these guardians must fortify their defenses.
Safeguarding mobile applications and upholding the highest standards of cybersecurity is not just a duty but a necessity. With a proactive approach, robust root detection mechanisms, and continuous vigilance, you can navigate the intricate landscape of vulnerabilities and ensure the security of your mobile applications.
References:
https://redfoxsec.com/blog/android-root-detection-bypass-using-frida https://www.indusface.com/learning/how-to-implement-root-detection-in-android-applications/https://www.cloudflare.com/learning/ssl/what-is-ssl/