External Penetration Testing – Case Study
ABSTRACT
External Penetration Testing consists of a reviewing and assessing the vulnerabilities that could be exploited by external users/Hacker without any credentials or without having any access to target system.
The assessment basically plays vital role in ensuring perimeter security, infrastructure security of the organization which may or can leads to the impact of business as Sensitive information present. Also it will ensure about possibilities of external threats/attackers & behavior of them as well, to minimize risk and threat ratio External Network Security Assessment has taken into consideration.
If External Network Security is not taken seriously, will leads to information/data theft which will be damage to the image of the company/organization’s brand and ultimately it will affect whole business of the organization. This will show whether there has been a Return on Investment (ROI) of existing implemented security controls, such as firewalls, intrusion detection and prevention systems, or implemented application defenses.
The role of a pentester is to perform penetration testing of the internet facing network, find vulnerabilities and try to exploit vulnerable systems/network to obtain confidential and sensitive information which can or may compromise the network perimeter and suggest measures to remediate the security issues to secure the network.
Varutra’s penetration testing methodology is in accordance with best standards and follows guidelines from OSSTMM, OSINT, NIST and OWASP. It makes use of our extensive experience in penetration testing and security assessment to discover previously missed vulnerabilities providing an impact level of security assurance.
This is a case study of an external network penetration test that Varutra performed on one of the overeas client organization proving egovernance. Some of the information has been changed or modified to maintain confidentiality.
BACKGROUND
The client network was consisting of various technologies such as firewall, routers, IPS, web servers etc. The goal was to understand the current level of external risks which may compromise the sensitive data of the customer as well as the organization. Mainly we had to understand about infrastructure of client network & based on it we started the Penetration Testing. Client commissioned Varutra to carry out an external penetration testing and supplied Varutra with the external IP address ranges to be tested. No other information given such as live IP addresses, name, type, nature of systems along with the underlined services running on them.
APPROACH AND METHODOLOGY
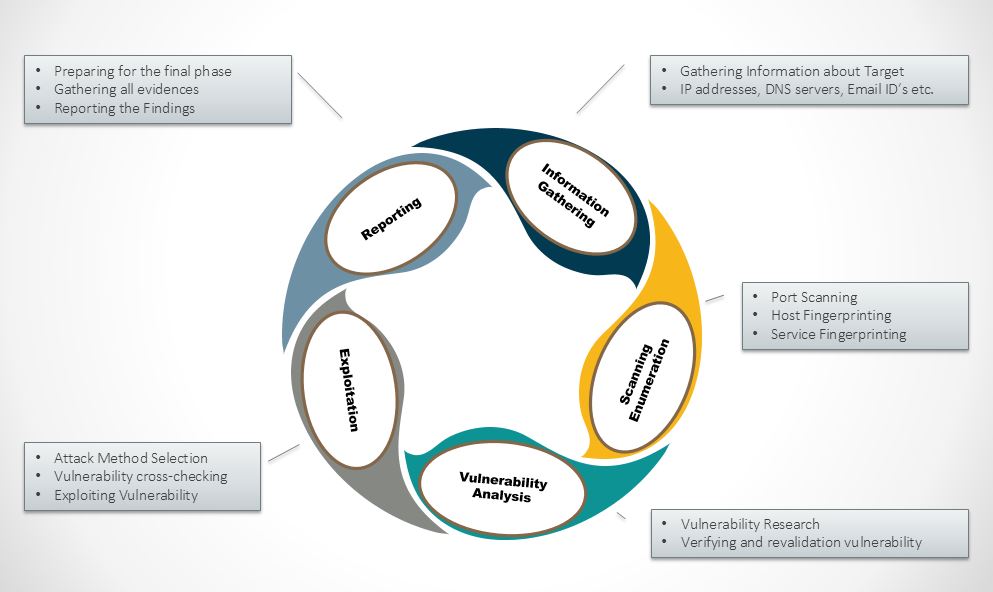
Varutra consultants then proceeded with the following stages of the penetration test:
Information gathering (Active & Passive)
– Attacking on DNS
– Discovering Firewall & IPS
– Scanning for External IP’s and associated systems, services.
Attacking WordPress application
Attacking Joomla application
Attacking Web Servers
– Attacking Web Applications
– User Account Bruteforcing
Attacking Network Layer
– Attacking Web Servers
– Attacking Email Server
– Firewall Evasion
Producing a detailed report of issues and recommendations with proof of concepts screenshots
Varutra has followed scenario based assessment approach for the Penetration Testing Phases.
During an External Penetration Test, Varutra can take the perspective of a known or unknown external threat to the organization. Varutra has started footprinting of the organization using Open Source Intelligence (OSINT), Domain Name System (DNS) reconnaissance, NSLookup and other techniques to identify all information that belongs to the client’s network & infrastructure. Varutra started identifying and discovering ports with respect to its services on each workstation and identified vulnerabilities associated with them.
During the attack phase, Varutra attempts to find all possible ways which can breach client’s network using the combinations of tools and techniques employed by hackers in real world attacks. Mainly targets includes web applications/web servers, email system, firewalls and personal information through techniques of Social Engineering attacks.
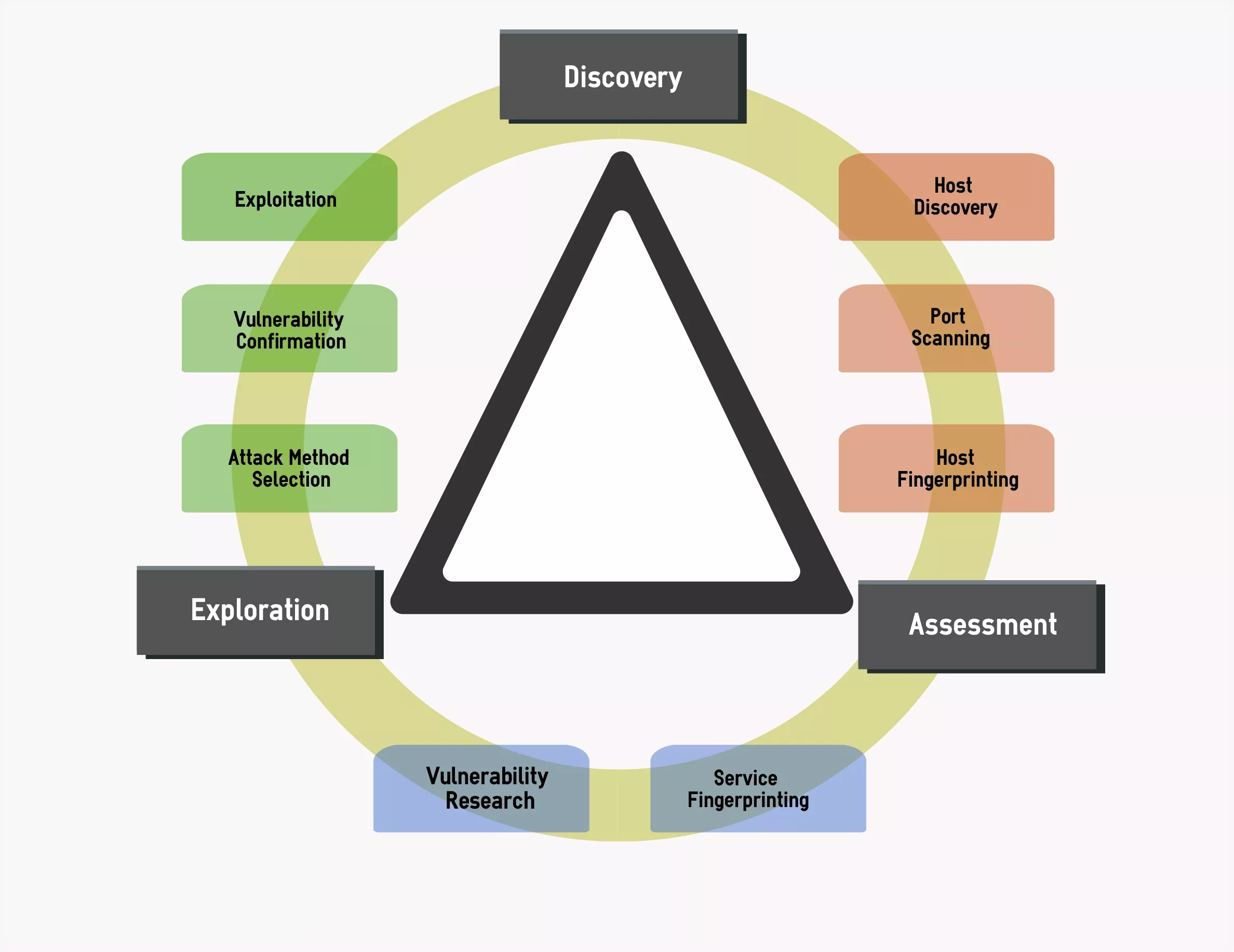
Figure: External Penetration Testing Methodology
KEY FINDINGS/OBSERVATIONS
Varutra identified and analysed network perimeter based on the scanning techniques and responses getting from the target. Identified firewall IP which was giving wrong information regarding ports i.e. firewall was misconfigured showing closed ports as well. While doing web server assessment we came across web-server running with outdated version of Apache which leads us conducting Denial of Service attack on the web-server. The attack was successfully achieved. On the web application layer Varutra found multiple critical vulnerabilities such as SQL Injection, XSS, HTML Injection, and Improper Session Management as well as some low and informational level vulnerabilities. This all assessment done with the automated testing using commercial and open source tools as well as extensive manual testing for verification and validation. This was the most important phase of a penetration test because it effectively demonstrates the impact of breach for the concern organization. Main targets in this phase were security credentials and other personal information, web-server/website credentials and sensitive proprietary information of organization (such as source code, or internal methodologies and formulas).
In the final deliverable, Varutra has provided in detailed information for each and every vulnerability which was discovered and exploited, including suggested recommendation or mitigation steps. Finally, Varutra has provided a detailed step-by-step impact of the breach to target organization which explains how several low severe vulnerabilities also can be linked together to achieve a complete and successful compromise.
KEY HIGHLIGHTS
Varutra consultants completed Penetration Testing process with scenario based. Main key highlights of the testing are listed below:
1. Initial scoping of the network was conducted to map and identify the current network, sensitive assets, entry points, existing security mechanisms etc.
2. Conducted penetration testing on the target network devices and systems.
3. Exploit tests carried out, such as mail spoofing and DNS zone transfer.
4. Consultants leveraged on the known vulnerabilities to further penetrate the network and identify the impact of the vulnerabilities if getting exploited.
5. Technical, in depth list of issues listed and recommendations on reducing the risk starting with the most critical.
DELIVERABLES
The reports and remediation information provided by Varutra were customized to match the Client’s operational environment and requirement. The following reports were submitted to the client:
1. Executive Report: Overview of the entire engagement, the vulnerabilities statistics and the roadmap for the recommendations made to mitigate the threats identified.
2. Technical Report: Comprehensive information, proof of concept examples and detailed exploitation instructions of all the threats/vulnerabilities identified and remediation for the same.
3. Mitigation Tracker: Simple and comprehensive vulnerability tracker aimed at helping the IT asset owner/administrator to keep track of the vulnerabilities, remediation status, action items, etc.
BENEFITS
Our Penetration Test helped the client to identify the potential threats / vulnerability that could have compromised their network and its components. We also assisted them in assessing percentage of potential business and operational impacts of successful attacks/exploitation.
Additionally, the client gained the following benefits:
* Risk Benefits: Varutra minimized security risks by assessing and analysing the client’s infrastructure vulnerabilities and recommended solutions and remediation with proven methods to enhance security of organization.
* Cost Savings: Varutra suggested cost-effective risk-mitigation measures based on the client’s business requirements that would ensure security and continuity of the business.
* Customer Satisfaction: Penetration testing was conducted with minimum interruption and damage across client systems/workstations to identify security vulnerabilities, their impacts and potential risks.
* Compliance: As an added bonus, the client was able to utilize the information gained from this Penetration Test to easily gain industry certifications and provide a higher level of service to its customers.
REFERENCES
https://www.dionach.com/library/network-penetration-test-case-study
http://www.testlab.com.au/images/pentest.png
AUTHOR:
Omkar Joshi & Chetan Gulhane
Security Consultant, Varutra Consulting Pvt. Ltd.