What is Computer Forensics & Its Types?
Computer Forensics Computer forensics is a process of identifying, preserving, analyzing, and presenting digital evidence in a legally acceptable manner. It Invоles оbtаining аnd аnаlyzing…
The Importance of Zero Trust Network Access (ZTNA) in Healthcare
There has been a significant increase in data breaches worldwide in all industries, and the healthcare industry is no exception. Critical Insight’s 2021 healthcare data…
Access Control Vulnerabilities
This blog aims to understand and demonstrate different access control vulnerabilities. The flow here will start with the theoretical explanation of what access control is…
Navigating Top 5 Network Security Challenges With Zero Trust
Gone are the days when people regularly go to the office and work using the corporate network. Therefore, the hub-and-spoke network has branched out the…
7 Top Trends in Cybersecurity for 2022
The world is getting accustomed to digitalization, and the organization’s digital footprint is trending in cybersecurity for 2022. In short, these trends focus on: How…
5 Concerning Cyberattacks to Watch Out for in 2022
Introduction Technologies are evolving continuously, and we are primarily dependent on them. They make our day-to-day life easier, but they are also more prone to…
Exploit Kits: Attackers Preferred Exploitation Tools
Exploit Kits: Overview Cybercrime was once the domain of a tiny handful of people with excellent technical skills who leveraged their abilities for malicious acts….
Penetration Testing Using Metasploit Framework
Metasploit Framework is a powerful open-source penetration testing framework. You get to know all the information about penetration testing, IDS signature, and software vulnerabilities. It…
External Penetration Testing – Case Study
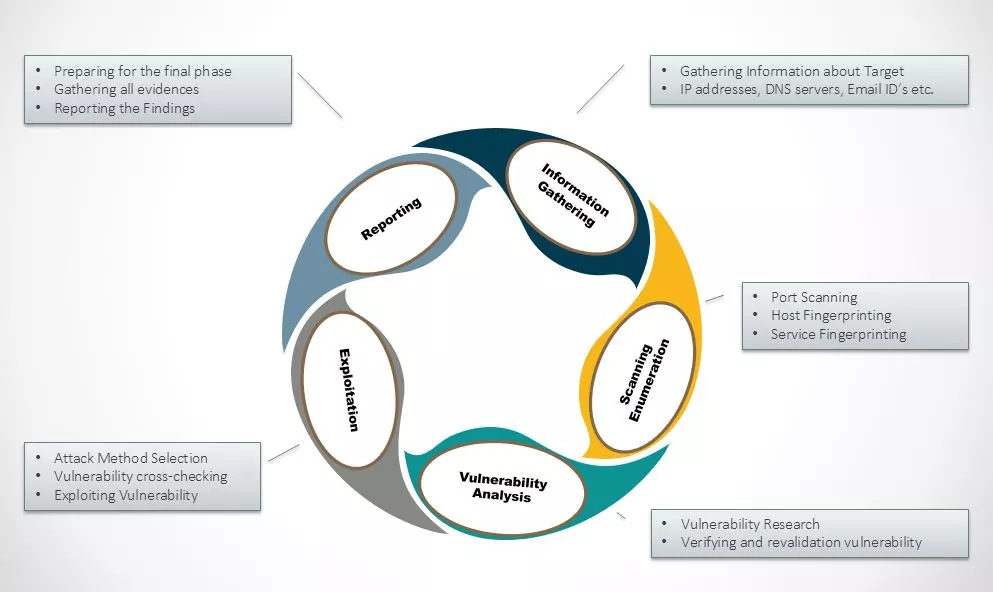
ABSTRACT External Penetration Testing consists of a reviewing and assessing the vulnerabilities that could be exploited by external users/Hacker without any credentials or without having…
VoIP Penetration Testing Part – IV
In the previous tutorial VoIP Penetration Testing Part – III we have learnt about SIP User extension enumeration. This is the last article in…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)