Access Control Vulnerabilities
This blog aims to understand and demonstrate different access control vulnerabilities. The flow here will start with the theoretical explanation of what access control is…
Why Ongoing Vulnerability Assessments Are Key to a Sound Security Posture?
Cybercriminals are very smart and continuously looking for opportunities to exploit any possible vulnerability they can find. In 2021, more than 50 vulnerabilities were logged…
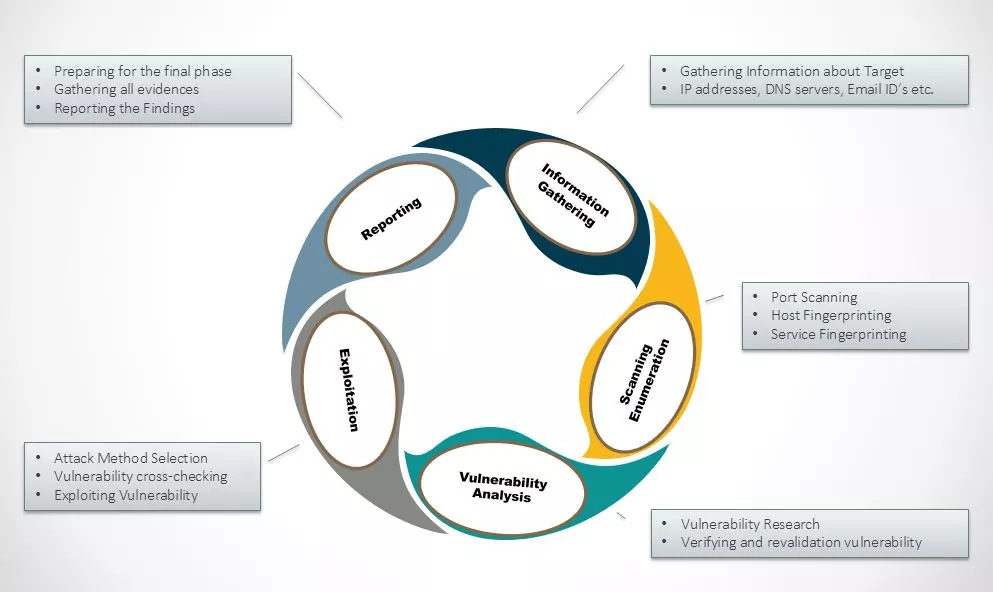
Penetration Testing Using Metasploit Framework
Metasploit Framework is a powerful open-source penetration testing framework. You get to know all the information about penetration testing, IDS signature, and software vulnerabilities. It…
Port Forwarding – Pivoting and Tunneling
Port forwarding is a key activity in any network security testing. Once we get an initial foothold into the victim network, our next stage is…
What Makes Penetration Testing Impactful – Post Exploitation
As a penetration tester, we often come across this riddle – What Makes Penetration Testing Really Impactful. As per penetration testing methodology – we identify…
Buffer Overflow Attacks
Introduction to Buffer Overflow Buffer is a storage place in memory where data can be stored. It’s mostly bound in a conditional statements to check…
External Penetration Testing – Case Study
ABSTRACT External Penetration Testing consists of a reviewing and assessing the vulnerabilities that could be exploited by external users/Hacker without any credentials or without having…
VoIP Penetration Testing Part – IV
In the previous tutorial VoIP Penetration Testing Part – III we have learnt about SIP User extension enumeration. This is the last article in…
VoIP Penetration Testing Part – III
In the previous tutorial VoIP Penetration Testing Part-II we have learnt on how to do scanning against VoIP Server. In this tutorial we will configure…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)