The Top 10 Mistakes to Avoid When Reviewing Source code
Are you making these crucial mistakes in your source code reviews? Our blog post reveals the top 10 mistakes that can undermine the effectiveness of your code review process. From failing to implement proper input validations to overlooking security vulnerabilities, these errors can have far-reaching consequences. Join us as we explore each mistake in detail and provide valuable insights on how to avoid them, ensuring the delivery of high-quality, error-free software.
Source Code Review: https://valuementor.com/blogs/source-code-review-why-and-when-why-is-it-important/
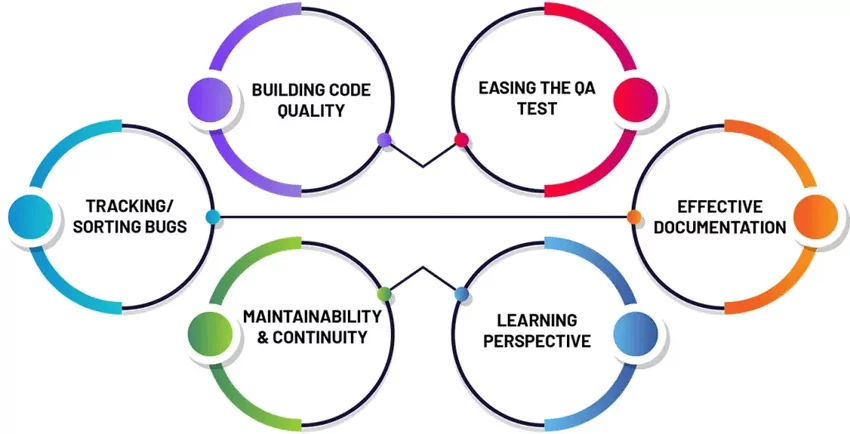
What is Source Code Review ?
Source code review is a critical aspect of ensuring effective and secure software development. By following best practices and avoiding common coding errors in code review, developers can identify vulnerabilities and enhance the overall quality of their code.

https://www.collidu.com/presentation-source-code-review
Top 10 Mistakes in Source Code Review:
Code reviews can find up to 90% of defects. A study by IBM found that code reviews found an average of 63 defects per 1,000 lines of code, while unit tests only found an average of 12 defects per 1,000 lines of code.
Here are the major errors that commonly occur in source code review.
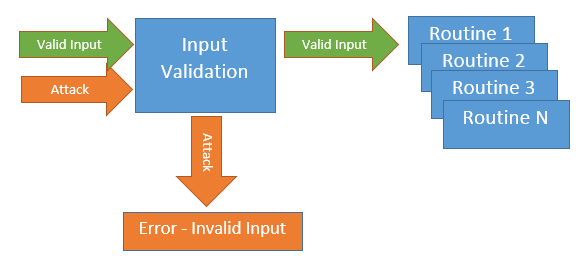
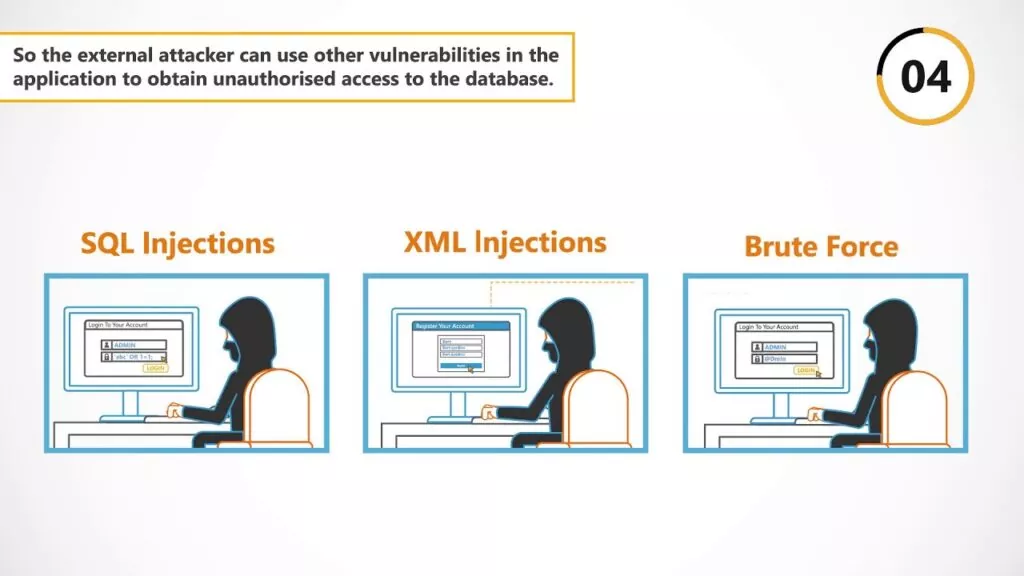
1. Lack of Input Validation:
One prevalent mistake in source code review is the absence or inadequate validation of user input. Failing to properly validate input leaves systems vulnerable to attacks such as SQL injection, buffer overflow, and cross-site scripting (XSS). Shockingly, according to a recent study, 40% of web applications have input validation vulnerabilities. Developers must validate and sanitize all user input, adhering to strict data validation rules.
Effective source code review techniques involve meticulous examination of input validation. By implementing code review tips and best practices for reviewing source code, developers can identify and rectify potential vulnerabilities caused by inadequate input validation.
https://securityintelligence.com/software-defenses-to-owasps-top-10-most-common-application-attacks/
To address this, developers should:
• Implement input validation routines at the earliest possible stage, using whitelisting or regular expressions to validate input.
• Prevent SQL injection attacks by using parameterized queries or prepared statements.
• Before displaying user-generated content to users, ensure to sanitize as well as escape it properly.
Example: In 2017, Equifax suffered a massive data breach due to insufficient input validation. Attackers exploited a vulnerability in the Apache Struts framework, resulting in the exposure of personal information of 147 million individuals.
2. Improper Error Handling:
When errors are not handled correctly, it becomes easier for attackers to glean valuable information about the system and exploit potential vulnerabilities. Developers should avoid revealing sensitive information in error messages and ensure that error handling mechanisms are robust, providing only essential details to users.
To address this, developers should:
• Avoid displaying detailed error messages to end-users, as they can reveal sensitive information about the system.
• Implement robust error handling mechanisms that log errors securely.
• Provide meaningful error messages to help developers identify and fix issues without disclosing sensitive data.
Example: The infamous 2013 Target data breach occurred due to poor error handling. Attackers exploited vulnerabilities in the network by stealing credentials from a third-party vendor. The lack of proper error logging and monitoring allowed the attackers to remain undetected for weeks.
3. Insecure Cryptographic Storage:
Secure storage of sensitive information is crucial for protecting user data. However, cryptographic flaws are often discovered during source code review. A shocking example is the Heartbleed vulnerability, which exposed OpenSSL’s weak implementation of the Transport Layer Security (TLS) protocol. Developers must follow industry best practices and use strong encryption algorithms, secure key management, and proper data storage mechanisms to mitigate the risk of data breaches.
(https://www.youtube.com/watch?v=wJOoUswXuRc)
To address this, developers should:
During the code review process, it is crucial to identify insecure cryptographic storage practices. By following code review tips and adopting secure coding practices, developers can ensure that sensitive information remains protected.
• Use strong encryption algorithms such as AES or RSA for data storage.
• Employ proper key management techniques, including securely storing and rotating cryptographic keys.
• Refrain from utilizing encryption algorithms that are weak or outdated.
Example: In 2015, the Ashley Madison data breach exposed the personal information of millions of users. The breach was possible due to the insecure cryptographic storage of passwords, which were hashed using weak algorithms.
4. Insecure Communication:
When sensitive information is transmitted across networks, it is essential to ensure secure communication. Unfortunately, insecure protocols and configurations are still prevalent. The POODLE vulnerability, for instance, exposed the security flaws in the SSLv3 protocol. Code reviewers must scrutinize the use of encryption protocols and ensure the adoption of secure alternatives like TLS. Additionally, developers should verify the appropriate use of encryption and secure configurations for network communications.
To address this, developers should:
• Employ robust security protocols like TLS or HTTPS for secure communication.
• Disable outdated and vulnerable protocols like SSLv3.
• Implement strong cipher suites and enforce certificate validation.
Example: The 2014 Yahoo data breach compromised the personal information of half a billion users. The breach occurred due to weak encryption and outdated communication protocols.
5. Insecure Authentication and Authorization:
Code reviewers must pay careful attention to ensure that robust authentication processes are in place, including secure password storage, multi-factor authentication, and secure session management. Similarly, authorization mechanisms should be thoroughly reviewed to prevent privilege escalation and unauthorized access.
To address this, developers should:
• Implement strong password policies, including enforcing password complexity and multi-factor authentication.
• Use secure session management techniques and prevent session hijacking or fixation attacks.
• Regularly review and update user privileges to prevent unauthorized access.
Example: The 2018 Cambridge Analytica scandal highlighted the importance of secure authentication and authorization. Improper access controls allowed unauthorized access to vast amounts of Facebook user data.
6. Insufficient Logging and Monitoring:
Inadequate logging and monitoring practices limit the visibility into system activities and can hinder timely detection of security incidents. Code reviewers should verify that the system adequately logs critical events and potential security-related activities. Additionally, it is crucial to establish a robust monitoring infrastructure that includes real-time alerting, anomaly detection, and response mechanisms.
To address this, developers should:
• Implement comprehensive logging mechanisms that capture relevant security events.
• Integrate log analysis tools to detect anomalies and security-related patterns.
• Set up real-time alerting mechanisms for immediate incident response.
Example: The 2013 Neiman Marcus data breach went undetected for several months due to inadequate logging and monitoring practices. Attackers had access to customer payment card information during this time.
7. Insecure Configuration Management:
Misconfigured systems are a goldmine for attackers. Incorrectly configured security settings can leave systems exposed and vulnerable. During code review, special attention should be given to reviewing configuration files, ensuring secure default settings, and minimizing attack surface areas. Regular audits and configuration management processes can help mitigate these risks.
To address this, developers should:
• Regularly review configuration files for secure default settings.
• Minimize attack surface areas by disabling unnecessary services and closing unused ports.
• Implement secure configuration management practices, including regular audits and vulnerability scanning.
Example: The Capital One data breach in 2019 was caused by a misconfigured web application firewall. The misconfiguration allowed an attacker to access sensitive customer data stored in the cloud.
8. Insecure Software Design:
The foundation of a secure software lies in its design. Poorly designed applications often contain inherent security flaws that are difficult to address in later stages. Code reviewers must evaluate the overall software architecture, identify potential design flaws, and ensure adherence to secure coding principles. By addressing security concerns during the design phase, developers can prevent vulnerabilities from seeping into the codebase.
To address this, developers should:
• Follow secure coding principles and best practices from the early stages of software development.
• Conduct threat modeling exercises to identify potential design flaws and security risks.
• Regularly review and update the software architecture to address emerging security concerns.
Example: The 2017 WannaCry ransomware attack exploited vulnerabilities in the Microsoft Windows operating system. The design flaws and weak security measures allowed the malware to spread rapidly across networks.
9. Insecure Software Deployment:
Secure software development extends beyond the source code itself; the deployment process also plays a critical role in maintaining the overall security of the system. Insecure software deployment practices can introduce vulnerabilities and weaken the system’s defenses.
To address this, developers should:
• Ensure secure update mechanisms to prevent the deployment of vulnerable or outdated software.
• Implement secure configurations for production environments, including access controls and secure network configurations.
• Safely handle and protect secrets and credentials, such as encryption keys and API tokens.
Example: The SolarWinds supply chain attack in 2020 targeted the software deployment process. Attackers injected malicious code into the software build process, allowing them to gain unauthorized access to numerous organizations’ systems.
10. Inadequate Security Testing:
Last but not least, insufficient security testing is a grave mistake often made during source code review. While functional testing is important, it is equally crucial to perform thorough security testing to identify vulnerabilities that could be exploited by attackers.
To address this, developers should:
• Integrate security testing at every stage of the software development lifecycle for comprehensive security measures.
• Conduct regular penetration testing to identify vulnerabilities and assess the system’s resilience to attacks.
• Utilize automated code analysis tools to identify potential security weaknesses.
Example: The 2017 Uber data breach occurred due to inadequate security testing. Attackers exploited a vulnerability in an external system to gain access to personal information of 57 million Uber users.
Conclusion:
Source code review is an indispensable part of developing secure software. However, even the most experienced professionals can make mistakes if they are not aware of common pitfalls. By addressing the ten common mistakes outlined in this blog post – lack of input validation, improper error handling, insecure cryptographic storage, insecure communications, insecure authentication and authorization, insufficient logging and monitoring, insecure configuration management, insecure software design, insecure software deployment, and inadequate security testing – developers and code reviewers can significantly enhance the security posture of their software.
Software security is an ongoing process that requires a proactive mindset and continuous vigilance. By staying updated with the latest security best practices, leveraging industry-standard security frameworks, and conducting regular code reviews, you can reduce the risk of security breaches and protect your software and users from potential harm.
Stay secure and keep coding!
Sources:
https://www.csoonline.com/article/567833/equifax-data-breach-faq-what-happened-who-was-affected-what-was-the-impact.html
https://www.theguardian.com/technology/2017/nov/21/uber-data-hack-cyber-attack
https://www.simplilearn.com/tutorials/cryptography-tutorial/all-about-solarwinds-attack
https://www.kaspersky.com/resource-center/threats/ransomware-wannacry
https://www.techtarget.com/searchsecurity/news/252521775/Paige-Thompson-found-guilty-in-2019-Capital-One-data-breach
https://www.nytimes.com/2014/01/24/business/neiman-marcus-breach-affected-1-1-million-cards.html
https://en.wikipedia.org/wiki/Facebook%E2%80%93Cambridge_Analytica_data_scandal#:~:text=While%20Cambridge%20Analytica%20claimed%20it,people%20from%20the%20United%20States
https://www.nytimes.com/2016/09/23/technology/yahoo-hackers.html
https://www.nytimes.com/2015/08/20/technology/the-ashley-madison-data-dump-explained.html
https://cardconnect.com/launchpointe/payment-trends/target-data-breach
https://www.codegrip.tech/productivity/common-code-review-mistakes/
https://talent500.co/blog/4-code-review-mistakes-and-how-to-avoid-them/
https://owasp.org/www-project-top-ten/
https://medium.com/swlh/top-ten-mistakes-found-while-doing-code-reviews-b935ef44e797
https://levelup.gitconnected.com/10-common-mistakes-developers-make-when-reviewing-code-81b042c3d642
https://blog.codacy.com/top-mistakes-code-reviews/
https://studysection.com/blog/common-code-review-mistakes/
https://google.github.io/eng-practices/review/reviewer/looking-for.html
https://snyk.io/learn/code-review/
https://www.decipherzone.com/blog-detail/secure-coding-practices/