Top 7 Cyber Security Measures That Enterprises Shouldn’t Neglect

India is considered the 3rd largest global hub with more than 5000 tech start-ups, and it is estimated that this number will grow 2.2x times in the coming three years. Unfortunately, India has experienced some worst cyberattacks in history, which have cost more than $5 million in the past two years. These cyber-attacks have targeted the financial, IT & telecommunication, healthcare, and retail sectors. It is said that 95% (IBM Survey) of hacks occur due to human error. In this blog, you will read about the top 7 cyber security measures that will help an organization keep their business and clients’ data secure.

Cyber Security Measures That Enterprises Shouldn’t Neglect
Here are the top 7 cyber security measures that an organization should follow to prevent cybersecurity risks.
Cyber Security Awareness Among Employees
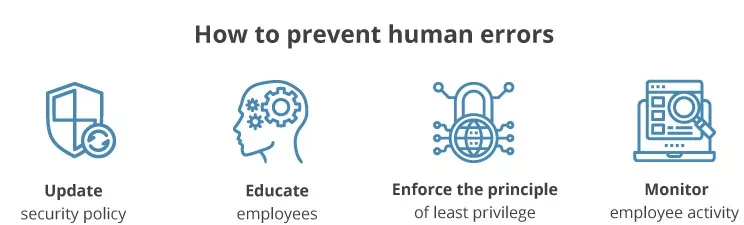
A famous quote, “Charity begins at home” similarly, security should also begin at home. If an organization wants strong protection, they need to start with its employees first. Even if an organization has the best WAFs, firewalls, antivirus software, and more, it will all be useless if the employee is not well-aware of the security measures to protect themselves. There should be strong security policies that employees should adhere to prevent hackers from exploiting the organization’s vulnerabilities. Unfortunately, no scanners will successfully identify 100% human errors. An organization should conduct regular training sessions to educate their employees about previous cyber-attacks and healthy security practices. Learning about past security statistics will help them understand the seriousness of the situation and help them protect themselves better.
Creating Strong and Secure Passwords
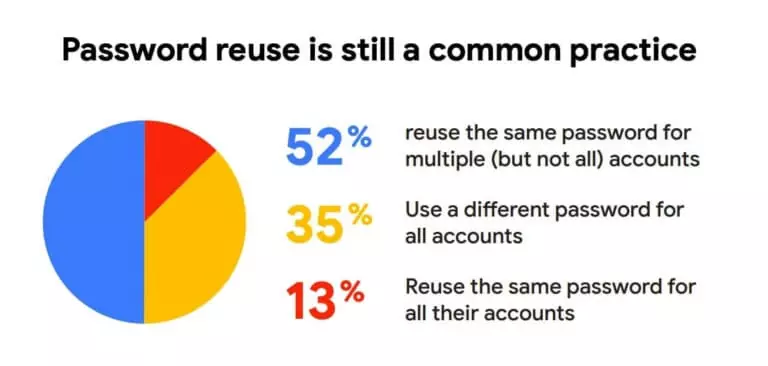
It is recommended that employees should change their passwords on a regular period. According to a survey, 35% of users have weak passwords like abcdef, 123456, 11111, or more, and the other 65% can be cracked easily. In addition, many users keep the same passwords for all their accounts, i.e., office and personal accounts. It makes them more vulnerable to cyberattacks. If their private account, like their social media account, is compromised, then there are chances that their other accounts can be easily hacked. This problem is one of the significant security issues with several organizations.
Following the Clean Desk Policy Everywhere
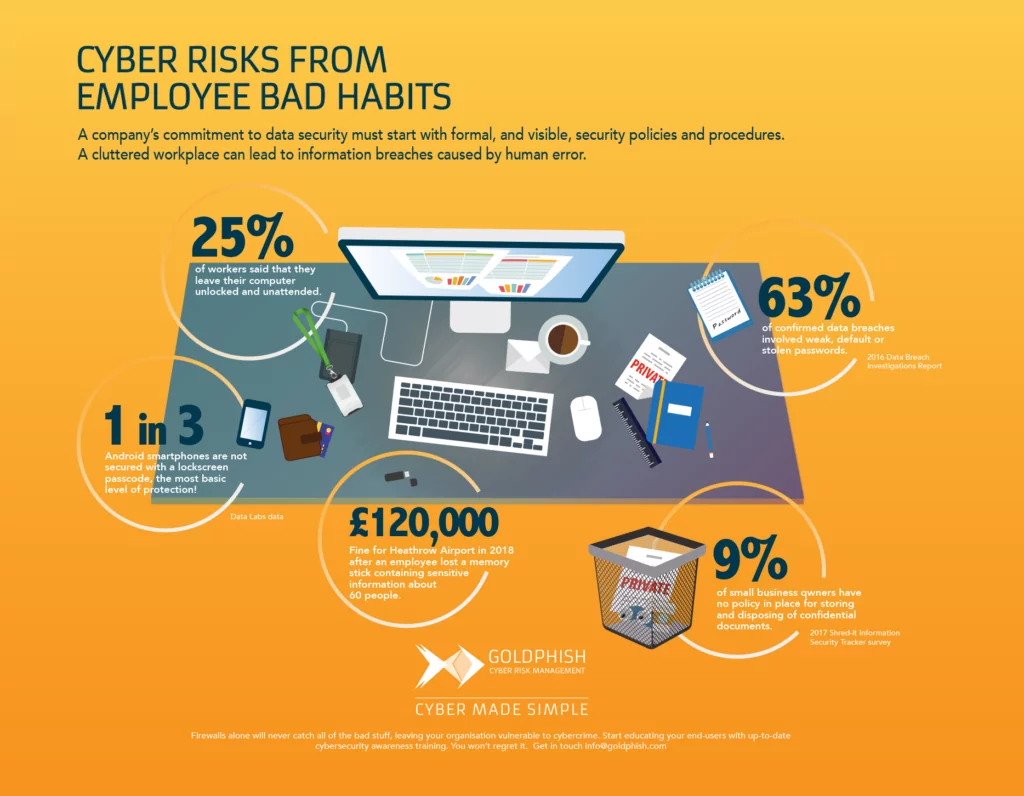
As per a recent survey, 24% of systems are not secured by the updated versions of antivirus software, making them 5.5 times more vulnerable to ransomware and virus attacks. The world-famous WannaCry ransomware is the perfect example of this scenario. It targeted the windows OS system that had not missed its security update from March 2017. It affected more than 100 countries and cost around $8 billion globally across the major industrial sectors. Therefore, it is recommended that the employees update their system, firewall, and antivirus applications regularly so that any vulnerability can be patched.
Thinking Ahead of Traditional Cyber Security Measures and Practices
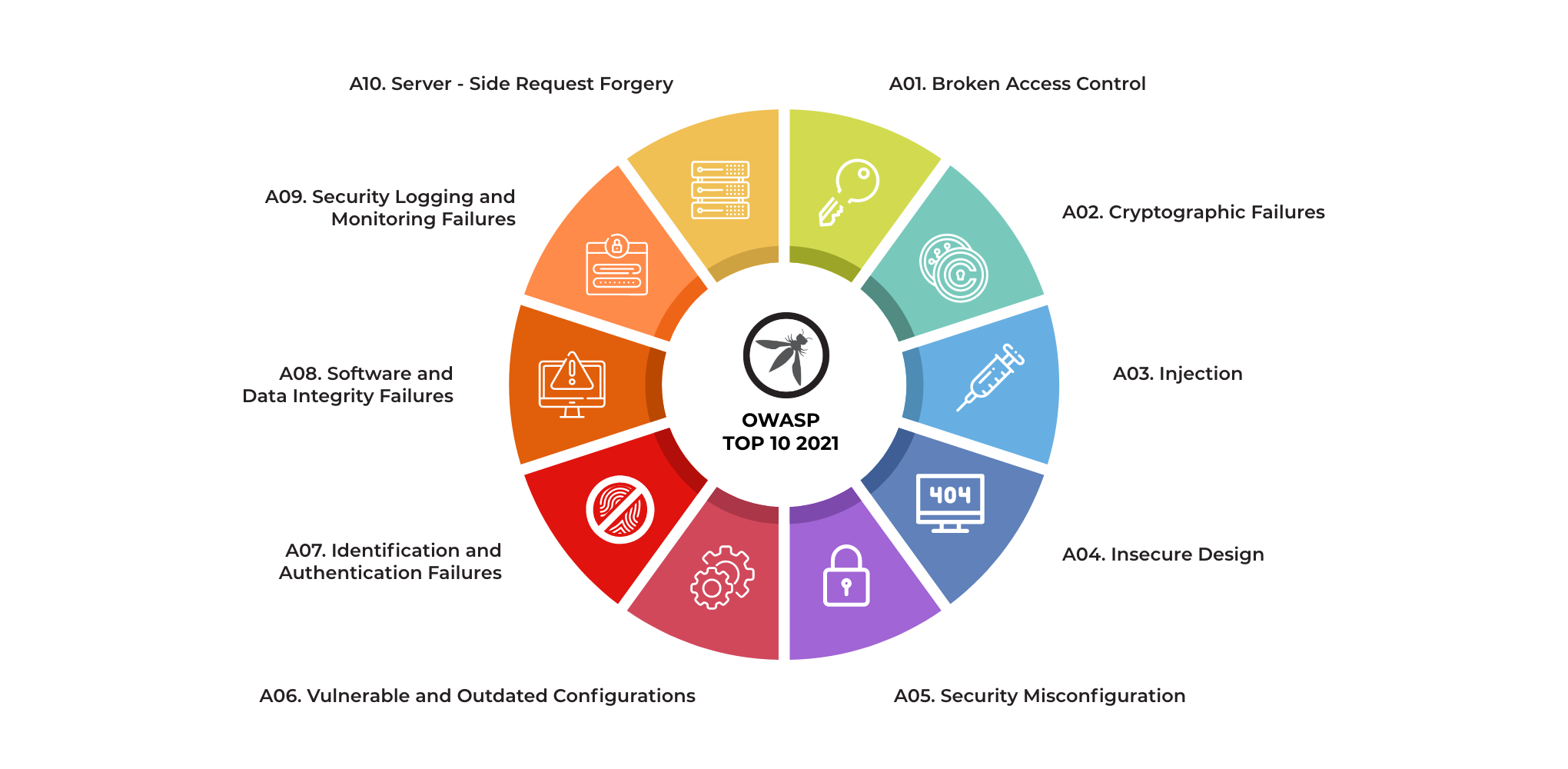
The cybersecurity testing begins and ends with VAPT (Vulnerability Assessment and Penetration Testing). Many companies just run the Vulnerability assessment and submit the reports to their clients to cut down the cost of testing. However, the organization is endangering its digital assets by cutting short the procedure. Various tools like Nexxus, Acutenix, Burp Suite, Netsparker, and more can help carry out the Vulnerability Assessment procedure. In addition, conducting manual penetration testing and following the OWASP Top 10 and SANS 25 guidelines will help identify 40% more vulnerabilities.
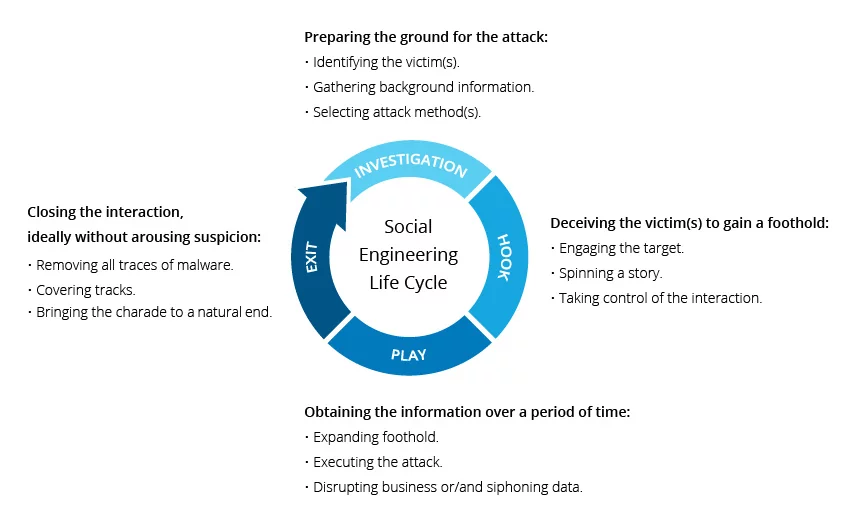
Conducting Social Engineering Activities and Red Team Exercises
Red Team Assessment is an exercise that helps in compromising the target at the entry point. It is an object-oriented activity that involves the participation of people, processes, and technology. Gaining access to the PII data of the customers, login credentials of the admin and non-admin personnel, hacking the account, compromising the CXO mailbox, and more is their primary objective. First, hackers will carry out VAPT manually to identify the infrastructure’s vulnerabilities. If they fail to identify the vulnerabilities manually, then they will target the individuals by carrying out social engineering activities like phishing attacks to fulfill their objectives. If they fail again, they try to physically enter the premises by tailgating and entering the server rooms to get access to the server rooms. This activity gives the business impact of a real-time cyber-attack and is used as an example of a cyber drill to create awareness among the employees.
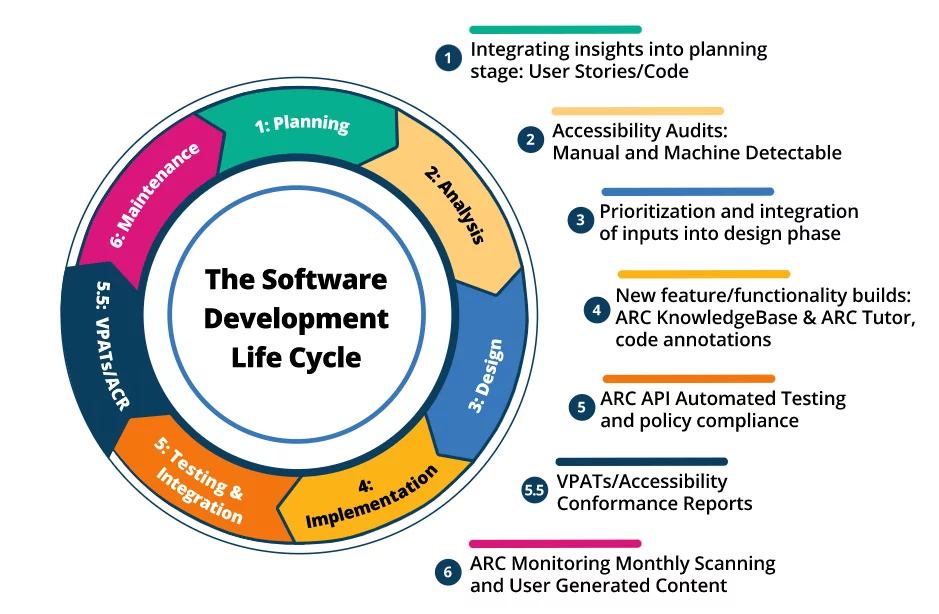
Secure SDLC (Software Development Life Cycle) Should Be Mandatory
Technology is getting advanced day by day. Several open-source in the market can build any application in just a few minutes. For a strong security foundation, the organizations should start working on their security until the deployment stage. A risk assessment should be performed in the analysis and requirement phase, and a secure requirement review should be followed after that. Next is the design phase, where you need to carry out threat modeling and get the architecture and design review for the same. As you reach the development phase, you will need your developers to work freely on the third-party libraries with default vulnerabilities. So, it is suggested that you perform dependencies check to identify the 60% OWASP vulnerabilities. You are in the QA testing phase, so you will need to complete the static analysis and secure your source code review for your applications simultaneously. When you finally reach the deployment phase, you need to perform the aggressive VAPT for the application and block the remaining vulnerabilities. Security is not a one-time activity. One should always test the application in pre-pod mode and resolve the vulnerabilities regularly to maintain a healthy and secure infrastructure.
Secured Cloud Computing and Configuration
Organizations are gradually moving to the cloud to save their bulk data. There are various leading cloud hosting providers like Amazon AWS, Microsoft Azure, Google Cloud, etc. They are cost-effective, provide unlimited storage, hassle-free backup, seamless software integration, great recovery options, etc. However, if your cloud is not integrated correctly, your data will be open to the public, and it won’t matter which cloud hosting services you are using. Therefore, proper configuration of the cloud is necessary, and performing a cloud security assessment is helpful. So, completing the security audit will help the organization uncover the misconfigurations in security groups, issues with cloud credentials, overly permissive IAM policies of users, etc. Possessing a solid deployment will help them identify misconfigurations in security and add an extra layer of protection to your cloud.

Conclusion
It is always recommended that an organization get assistance from an independent cybersecurity agency for reviewing and providing security to your applications. The few common mistakes in an organization due to negligence or lack of knowledge while developing a product can prove fatal. It will be vulnerable and can be exploited by hackers anytime. Varutra offers various cybersecurity services across the globe as per your requirement and decreases the chances of any potential cyber-attack that you may encounter in the future.
Reference
https://www.techtarget.com/searchsecurity/feature/Ten-ways-to-prevent-insider-security-threats
https://www.ekransystem.com/en/blog/best-cyber-security-practices
Author,
Sanjana Yadav,
Marketing Department,
Varutra Consulting Pvt. Ltd.




