WebSocket Vulnerabilities

This blog is about different types of WebSocket Vulnerabilities/Findings. So, we will be discussing different types of flaws that may exist in WebSockets.
WebSockets are becoming more and more popular these days because of the simplicity they provide for the communication between the client and the server.
Firstly, let’s get a brief overview of the WebSocket protocol. The WebSocket protocol is an OSI application layer protocol that allows a client and a web server to interact in full duplex (a communication channel where information can flow in both ways at the same time).
Different Vulnerabilities/findings related to WebSockets:
While WebSockets are beneficial for generating full-duplex communication channels (in modern applications, the server may need to provide data to the client without the client making a special request, such as in instant messaging), they do not provide any further security benefits. As a result, we find the standard vulnerabilities of the HTTP protocol, as well as some unique ones.
- DOS:
WebSockets allow an unlimited number of connections to the server to be established. This feature will allow to make a lot of connections which in turn will put a lot of demand on the server and use up all of its resources. The webpage then becomes noticeably slower. This way, a DOS attack can be launched against the server.
- Cross-Site WebSocket Hijacking:
It is a type of CSRF (Cross-Site Request Forgery) attack. When the server relies entirely on session authentication data (cookies) to complete an authenticated action, these types of attacks are feasible.
The attacker hides a request in a link on the screen of its (authenticated) victim in CSRF. The attacker tricks the victim into clicking on it to carry out the hidden request’s request. As a result, the attacker has the ability to make the victim do something harmful without the victim’s knowledge. The problem is that the attacker cannot view the server’s response to the request (due to the origin policy), which is no longer a concern with WebSockets because it doesn’t employ an origin policy. The attacker can now establish a full-duplex connection using the victim’s credentials.
When the WebSocket handshake is vulnerable to CSRF, the Cross-Site WebSocket Hijacking attack is feasible. Indeed, the origin of the original application determines the communication channel between the two parties (client/server). As a result, if the protocol change request is entirely dependent on cookies, an attacker can lure a victim into starting a request with its session but based on the attacker’s server.
Once trapped, the attacker can use WebSockets to communicate with the server without the victim’s knowledge. As with a traditional CSRF, the attacker can take actions in the recipient’s place while also reading server communications delivered over WebSockets.
It is better to put a unique token per session that cannot be guessed as a parameter of the handshake request to mitigate this vulnerability.
- Sniffing Attacks:
The WebSocket protocol transfers data in plain text, same as HTTP. As a result, man-in-the-middle attacks on this data are possible. Use the WebSocket Secure (wss:/) protocol to avoid data leaks. WSS, like HTTPS, does not guarantee that your web application is secure, but it does assure that data is encrypted using Transport Layer Security (TLS).
- Input-Validation Vulnerabilities:
If the input validation on WebSocket user input is not proper, then Injection attacks targeting WebSocket vulnerabilities such as XSS, SQL injection, XXE, and others can be launched.
- Unauthorized access to WebSocket communication
It is possible to read and alter WebSocket communication at the network level if it is not established via the WebSocket over TLS (wss:/) protocol. To do this, attackers need to be in a privileged position on the network.
WebSockets don’t have any kind of authentication or authorization. Since no authentication is necessary to create a WebSocket, attackers can create their own connections and potentially access data that is only accessible via HTTP authentication. Attackers can obtain unauthorized access to information by sending WebSocket messages if access permissions are not checked within the connection.
These are some of the different vulnerabilities that were found in WebSockets.
Now, we will see the demo of one type of vulnerability i.e., Input-Validation Vulnerability. For demonstration purpose, let’s navigate to a Portswigger lab to see the exploitation.
Lab:
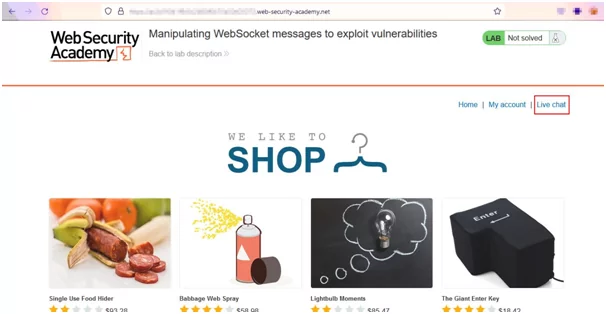
Step 1: Access the lab and go to the live chat page.
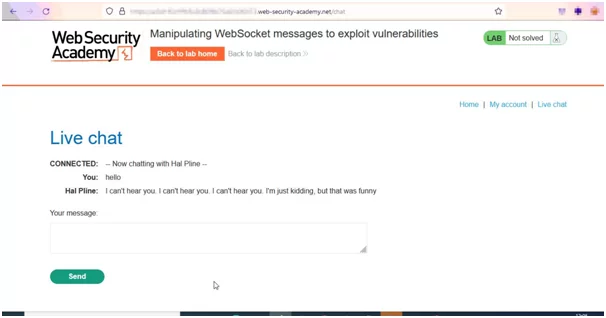
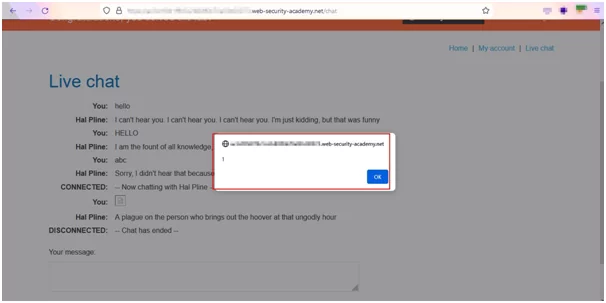
Step 2: In the live chat page, enter the message.
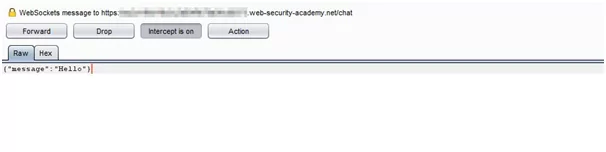
Step 3: Intercept the message request in Burp.
Step 4: In the intercepted request, enter the payload in the WebSocket message.
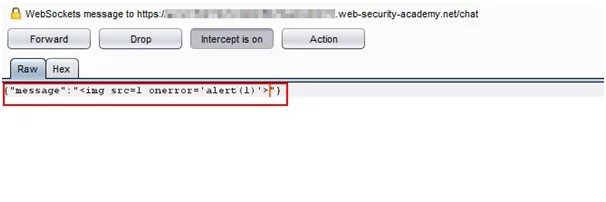
Step 5: Forward the request and the payload will be executed and you will get a pop-up in your browser.
Thus, the lab is executed. Here, we have bypassed the client-side input validation in the chat and executed the payload.
Mitigation/Prevention of Websocket Vulnerabilities:
Following some protective measures while using WebSockets will mitigate the above-mentioned vulnerabilities to some extent.
- Using wss:// (i.e., WebSockets over TLS).
- Check Origin header during handshake, use Access-Control-Allow-Origin header on server side.
- Using Nonce/CSRF tokens can protect the handshake against CSRF attacks.
- Using authentication for WebSockets would be beneficial, for example using a JSON Web Token.
- Performing validation on input messages in both directions.
- Encoding of output messages embedded in the application.
After getting to know much about WebSocket findings/vulnerabilities and how they can be exploited by attackers when proper security measures are not taken, it is essential to have appropriate security measures and mechanisms in place to ensure WebSocket communications remain secure. We can’t say the using the above suggested mitigation/prevention measures will make the use of WebSockets fully secure, but implementing these suggestions might minimize the risk to some extent.
Author:
Pralekya Hirmalwar
Attack & PenTest Team
Varutra Consulting Pvt. Ltd.



