Roadmap to FedRAMP Compliance
The basic layman’s concept behind cloud computing technology is that the user does not need to physically manage any server or hardware to process his data, Cloud computing is more like using someone’s computer resources remotely to perform and execute your task. Over the period the cloud computing has seen a steep rise in migration of users from On-Premise’s hosting platform to Cloud Hosting Platforms. The Cloud solutions are comparatively cheaper, and the users need not worry about the investment required for the use of NICHE technology.
According to Gartner, INC the worldwide end-user expenditure on public cloud platform services is predicted to forecast to rise by 18.4% in the year 2021 to a total sum of $304.9 billion, rising from a huge $257.5 billion even during the Covid Pandemic in 2020.
Just as the cloud computing platform has transformed the way many organizations and companies manage their infrastructure and IT assets and do business; the federal government has further recognized the impact that clouds computing platforms and services will have in re-structuring how they do business and perform operations as well as how they can save the commercial expenditure on federal IT infrastructure. The federal government has further identified the associated Threats – Risks that are a part of worry for processing the federal data on a cloud computing platform.
Thus, the federal government has established the process coined as FedRAMP – Federal Risk and Authorization Management Program, to address the federal information and data security concerns with respect to Confidentiality, Integrity, Availability, and reliability of cloud services that are used by the federal government, offices, and agencies.
What is FedRAMP Compliance?
FedRAMP was established in the year 2011 with a vision to provide a cost-effective and risk-based assessment approach for the incorporation and ease of use of cloud services by the federal government agencies. FedRAMP has empowered the agencies to use the modern state-of-the-art niche cloud technologies, with a mission and vision to safeguard the confidentiality – integrity, and availability of federal data.
For a commercial cloud service offering (CSO) to be used as a service by any federal agency, the CSO must be FedRAMP compliant to further adhere to the government security requirements that are outlined in NIST 800-53 Standard and supplemented by the FedRAMP Program Management Office (PMO).
In layman’s language, the cloud service providers (CSP) need to obtain a FedRAMP authorization, or FedRAMP Authority to Operate (ATO) to demonstrate his compliance with FedRAMP.
What is FedRAMP Security Assessment Framework (SAF)?
The CSP is assessed by the Federal Agencies based on the FISMA requirements. The FedRAMP SAF is based on and is compliant with FISMA which is further based on NIST Special Publication Standard 800-37.
FedRAMP has defined a set of control for Low and Moderate and High-security impact level systems based on NIST baseline controls (NIST SP 800-53, as revised) with a set of controls that pertain specifically to the security requirements of cloud computing technology.
FedRAMP uses the same documents and deliverables that NIST requires Agencies to use, as described in NIST SP 800-37. FedRAMP has simplified the NIST Risk Management Framework by creating four process areas around it that encompass the steps detailed within NIST SP 800-37: Document, Assess, Authorize, and Monitor as shown the below figure.
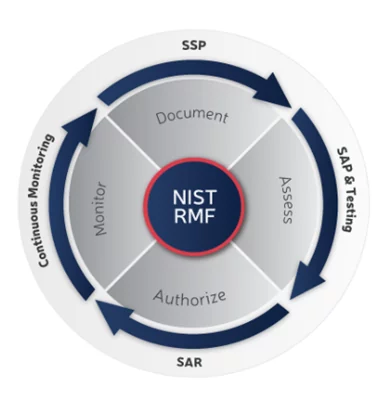
FedRAMP Risk Management Framework
- Document
CSPs have to categorize CSO as per and according to the FIPS-199. The resulting categorization of the evaluation based on FIPS – 199(Low, Moderate, or High) will determine the associated NIST 800-53 controls (and FedRAMP supplemental controls) that will apply to the CSO and need to comply with.
- Assess
For the Assessment, phase to begin the SSP and other required documentation need to be in place, reviewed, and approved. Post which a Third-Party Assessment Organization – 3PAO will come up with a security assessment plan (SAP) which outlines the testing approach for the CSO.
Once the SAP is approved by the CSO (and the counterpart federal agency for the ATO), the 3PAO will further test the implementation of controls and derive a Security Assessment Report (SAR).
- Authorize
During this phase, the SAR prepared by the 3PAO is reviewed by the federal agency (for an agency authorization) and approved. Once the SAR is approved by the Agency an agency ATO letter (for the agency path) is issued and uploaded to a secure controlled central repository with all other required mandatory documentation that is needed for FedRAMP Compliance. The FedRAMP PMO then further reviews these documentation sets and decides regarding the FedRAMP authorization.
- Continuous Monitoring
Once an initial agency ATO or JAB P-ATO is achieved by the CSP, the CSP enters the continuous monitoring phase. During this phase, the CSP ensures that the controls that were assessed by the Authorizing body will continue to operate effectively. A part of the implemented controls are monitored and evaluated at specified predefined time intervals and data regarding compliance status is provided to the authorizing agency duly.
What are the FedRAMP compliance requirements?
The high-level requirements to achieve FedRAMP compliance are as follows:
- The CSP should ensure and complete the FedRAMP Compliance required mandatory documentation including the FedRAMP System Security Plan (SSP).
- The controls as per the FIPS 199 categorization of the CSO are to be implemented.
- The CSP must be assessed by a FedRAMP Third Party Assessment Organization (3PAO).
- The findings are to be remediated if any are highlighted by the 3PAO during this engagement.
- A Plan of Action and Milestones (POA&M)must be developed.
- The Agency ATO or Joint Authorization Board (JAB) Provisional ATO (P-ATO) approval must be obtained.
- Process of continuous monitoring must be incorporated including the monthly scans for vulnerability.
Two Ways to Achieve FedRAMP Compliance
There are two ways that a CSP can take to obtain a FedRAMP authorization or an ATO(Authority to Operate). The first path is to obtain a FedRAMP ATO directly from a federal agency that you intend to provide service to. The second path is to receive a FedRAMP P-ATO from the JAB.
Agency ATO Vs JAB P-ATO
The major difference between an Agency FedRAMP ATO and a JAB P-ATO is the authorization scope or an ATO.
The Agency FedRAMP ATO is applicable and limited to that federal agency itself. And this does not further mean that the other federal agencies are authorized to use the services of that CSO. The different federal agencies have their different buckets of risk appetite and evaluation standards. So a CSO getting an Agency FedRAMP ATO from one agency will not be authorized to operate with the other agency unless and until he obtains that agency-specific FedRAMP ATO.
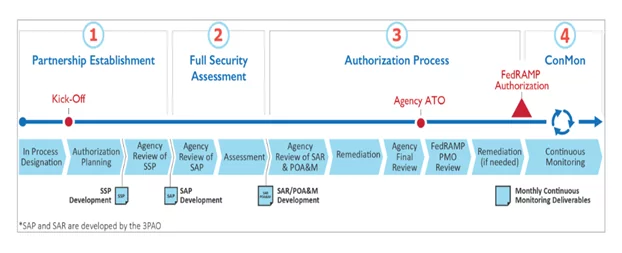
Agency Authorization Process RoadMap
Once a Cloud Service Operator has Agency FedRAMP ATO with a Federal Agency, and some other agency now wants to use the services of this CSO then the other Agency will evaluate the authorization packages with respect to the risk profile and appetite of the Agency and will determine if the, if the resulting assessment is and determined security posture of the CSO, is sufficient to meet the risk standards and the security requirements.
It this is found true, and the Authorization Packages are enough to handle and sustain the requirements of the new Federal Agency then the agency will issue the FedRAMP Authorization – ATO to the CSP for his CSO to the federal agency. And if it is not meeting the Authorization Standard Requirements then additional requirements and testing are needed to address the need of the new federal agency.
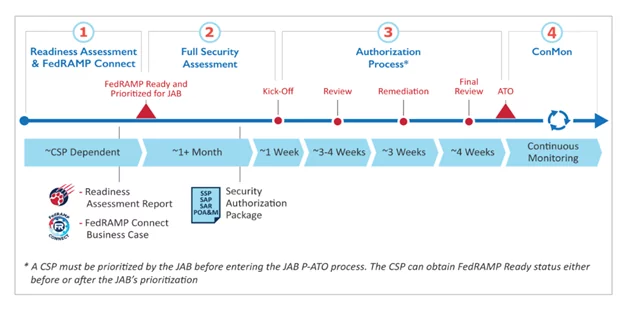
JAB Authorization Process Road Map
The JAB – Joint Authorization Board is the primary governing body for FedRAMP compliance regulations and includes the representative and stakeholders from the Department of Defense (DoD), Department of Homeland Security (DHS), and General Services Administration (GSA).
The JAB governing body selects approximately 12 cloud products or CSO a year to work with for a JAB Provisional Authority to Operate (P-ATO). The JAB is further responsible for performing the continuous monitoring for all JAB Authorized cloud products or CSO. The Authorization is a Provisional – ATO and this does not determine the risk acceptance and mitigation part of the Federal Agencies. Thus, to further operate or get associated with an Agency for a CSO, the CSO needs to obtain an ATO from the Agency.
Author,
Omkar Gaikwad
Audit and Compliance
Varutra Consulting Pvt. Ltd.




