Application Security
Overview:
This is the training one should go for if one needs to defend web applications both Web and Mobile! This training is divided into two domains –
1.Application Security Assessment
2.Application Source Code Review
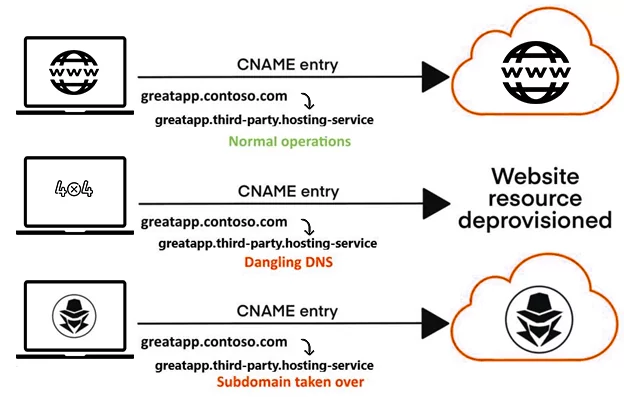
In Application security assessment, participants will learn how attackers break into web applications to obtain sensitive data and information, application server compromise, exploiting remote code execution vulnerabilities, and perform SQL Injection to denial of service attacks and many others.
Under Application Secure Source Code Review, participants will be able to identify security flaws in web and mobile applications before they go live. It covers the process of auditing the source code of an application, verify the implementation of adequate security controls and eliminate serious software flaws that may affect the confidentiality, integrity and availability of data.
The course will also cover additional out of the box vulnerabilities which our trainers have found in their day-to-day pentesting engagements.
Topics covered include:
- OWASP Top 10 Vulnerabilities (Web and Mobile)
- SANS Top 25 Programming Errors
- Application issues from the Common Weakness Enumeration (CWE)
- Web Services (REST/SOAP)
- Business Logic Testing
- Automated and Manual Code Review
Audience:
- Application Developers
- Application Security Analysts
- Application Security Architects
- Penetration Testers interested in learning offensive / defensive strategies
- Information Security professionals interested in learning application security
Pre-requisites:
- This training requires a basic understanding of how internet works, basics of web application technologies and concepts such as HTML and JavaScript.
- Participants to have their own laptop with minimum system configuration covering – 64-bit Intel i5 or i7 processor, 12 GB RAM, 250 GB minimum HDD free space, Windows 10 or macOS or Linux OS, and support for Virtualization technology.
- Testing lab and tools will be set on the 1st day of the training.
Duration:
5 Days (8 hrs/day)
+91 840 8891 911