Sweet32 Birthday Attack Approach

In this blog, we are going to understand one of the TLS/SSL attacks i.e., Sweet32 Birthday Attack Approach.
Mostly Sweet32 birthday attack is found in networks where block ciphers of smaller size are being used. Block ciphers are commonly used in protocols like TLS, SSH, IPSEC, Open VPN, etc. Popularly used block cipher algorithms in cryptographic protocols listed above are AES, Triple-DES, Blowfish, which are used to encrypt data between clients and servers.
Block ciphers will be the most common term that will be used throughout this blog. So first let us just get an idea of what is cipher, what is block cipher, and why are they used.
Cipher and Block Ciphers:
A Cipher is basically an algorithm or function which is used to encrypt and decrypt the data. There are many ciphers out there with different levels (range) of complexity.
Ciphers can be divided into different categories like substitution cipher, transposition cipher, Stream ciphers and block ciphers, etc.
Here we are particularly interested in block ciphers. So what exactly are block ciphers?
Block ciphers are a type of symmetric algorithm. As the name implies, rather than bit-by-bit these ciphers encrypt plaintext in blocks. Block length in ciphers determines the size of chunks into which the plaintext is split and after that, they will be encrypted. Block length is independent of the key size. Different modes of block cipher are CBC, CTR, GCM, OCB, etc.
Block ciphers are usually used with a specific mode of operation. These modes of operations are used to deal with the arbitrary length of messages.
Basically, CBC is a mode in block ciphers where the block is initially exclusively XOR’ed with the previous block of plain text and then it is encrypted. This resulted in the encrypted block is after that used for XORing and encrypting the next block of a cipher.
CBC is secure up to2^{n/2} block of message. CBC ciphers are mostly vulnerable to birthday attacks when the message is 2n/2 block of messages, and these messages are encrypted with the same key. In this case, a collision is most likely to happen between any 2 blocks of ciphertexts.
The birthday binding corresponds to 256 EB with a modern block cipher with 128-bit blocks such as AES. The birthday bound, however, corresponds to only 32 GB for a block cipher with 64-bit blocks, which is easily accomplished in practice.
At a time when 64-bit block ciphers, such as Triple-DES and Blowfish, were still deemed powerful, many of the most popular Internet security protocols, such as TLS, SSH, and IPsec, were standardized. For instance, in TLS 1.0 and 1.1, the mandatory encryption algorithm is Triple-DES, so it is implemented by all TLS libraries and supported by most web servers.
Before trying to understand what exactly the sweet32 birthday attack is and what happens in this attack, we will try to understand one of the algorithms that are vulnerable to the sweet32 birthday attack, and that is Triple-DES also called 3DES.
DES and Triple-DES algorithm:
Triple-DES is a symmetric key algorithm used to encrypt and decrypt plain-text data. 3DES has 2 types: one is 2 key 3DES and 3 key 3DES. Working of 3DES is shown using the flow chart shown below:
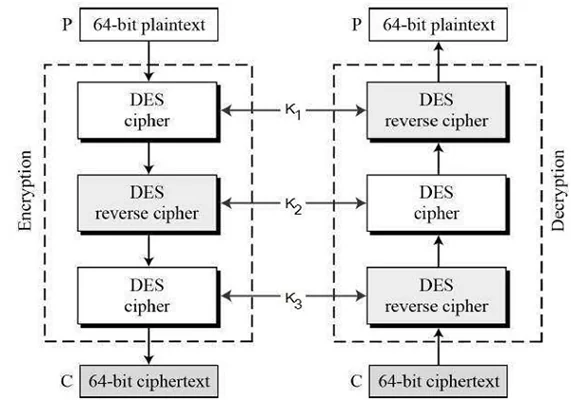
Fig: Encryption and decryption process in 3-key 3DES algorithm.
The encryption and decryption process in triple DES is as shown above in the figure, K1 is used in the first DES cipher, K2 is used in reverse DES, and K3 is used in the last step.
For 2 key 3DES, the first key the same 3step process is followed, the only difference is that the first step i.e. DES cipher uses K1, then the second step i.e. DES reverse cipher is performed using K2 and the last step i.e. DES cipher is performed uses K1. Hence we only need 2 keys K1 and K2.
Looking at the figure, we might think about what happens in DES and reverse DES.
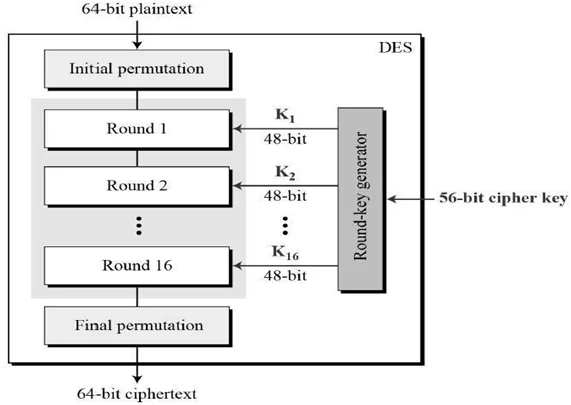
Fig: Working overview of DES algorithm.
The figure shows an overview of the working of the DES algorithm. Initially, a 64-bit plain text is given to the algorithm, which then processes the same to a 64-bit ciphertext. What happens in between the process is a bit tricky to understand. Let’s try to understand the working of DES now.
Firstly an Initial permutation is performed on the 64-bit plain text. The key in DES is originally is of 64-bit but a 56-bit key is used in the algorithm. By omitting every 8th bit in the key, a 64-bit key is converted into a 56-bit key. After there are 16 rounds of operation performed on the plain text. Once these 16 rounds are done, DES with performing the final permutation and a 64-bit ciphertext is finally obtained.
In those 16 rounds of encryption, the following process is followed.
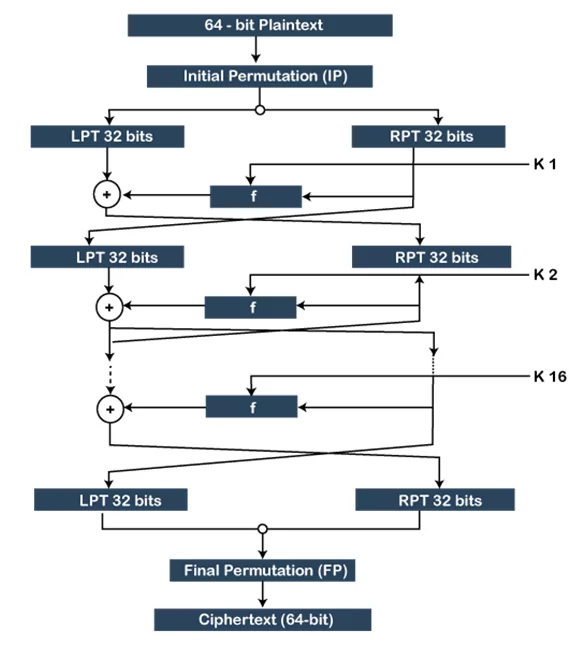
Fig: Detailed working of DES.
The above figure shows the process of DES along with the process of 16 rounds of encryption. After the Initial permutation, 16 rounds of encryption is done using the Feistel cipher structure. The plain text is divided into 2 equal parts, 32-bit Left plain text and 32-bit right plain text. The right plain text block is replaced as the Left plain text block in the next round of encryption, and also this block undergoes from some functions “f” which again is XORed with the left plain text and then is passed as the right plain text block for the next round of encryption. The second round of encryption can be represented as equations as follows:
- LPT1= RPT0
- RPT1= LPT0 ⊕ f(RPT0,K1).
After the completion of 16 rounds of encryption, a final permutation is performed and the 64-bit ciphertext is obtained as the final output of the algorithm.
This was a detailed explanation about the working of DES and 3DES algorithm. Now let’s move to Sweet32 birthday attack.
Sweet32 birthday attack:
The DES ciphers (and triple-DES) only have a 64-bit block size. This enables an attacker to run JavaScript in a browser and send large amounts of traffic during the same TLS connection, creating a collision. With this collision, the attacker is able to retrieve information from a session cookie.
This vulnerability could be used by a man-in-the-middle attacker to recover some plaintext data. The attacker is able to intercept vast volumes of encrypted traffic between the client and the TLS/SSL server.
A large number of HTTPS servers and all major web browsers, about 600 of the most-visited websites, support the triple-DES cipher. Fortunately, when creating an HTTPS link, most browsers tend to use AES rather than triple-DES.
Finding if the network is vulnerable to Sweet32 birthday attack:
To check if the network is vulnerable to the Sweet32 birthday attack, one of the methods is to use the Nmap command. The process of checking for sweet32 birthday attack using Nmap is stated below:
There is an nmap script available to check if the network is vulnerable to a sweet32 birthday attack:
Nmap script: nmap -sV –script ssl-enum-ciphers -p 443 <host>
By running the above-mentioned script we get the following output:
PORT STATE SERVICE REASON443/tcpopen httpssyn-ack| ssl-enum-ciphers:| TLSv1.0:| ciphers:| TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA (secp256r1) – A| TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA (secp256r1) – A| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (secp256r1) – A| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) – A| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) – A| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) – A| TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA (secp256r1) – C| TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA (secp256r1) – C| TLS_RSA_WITH_3DES_EDE_CBC_SHA (rsa 2048) – C| TLS_ECDHE_ECDSA_WITH_RC4_128_SHA (secp256r1) – C| TLS_ECDHE_RSA_WITH_RC4_128_SHA (secp256r1) – C| TLS_RSA_WITH_RC4_128_SHA (rsa 2048) – C| TLS_RSA_WITH_RC4_128_MD5 (rsa 2048) – C| compressors:| NULL| cipher preference: server| warnings:| 64-bit block cipher 3DES vulnerable to SWEET32 attack| Broken cipher RC4 is deprecated by RFC 7465| Ciphersuite uses MD5 for message integrity| Weak certificate signature: SHA1| TLSv1.2:| ciphers:| TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 (secp256r1) – A| TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 (secp256r1) – A| TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA (secp256r1) – A| TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA (secp256r1) – A| TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 (secp256r1) – A| TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (secp256r1) – A| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (secp256r1) – A| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) – A| TLS_RSA_WITH_AES_128_GCM_SHA256 (rsa 2048) – A| TLS_RSA_WITH_AES_256_GCM_SHA384 (rsa 2048) – A| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) – A| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) – A| TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA (secp256r1) – C| TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA (secp256r1) – C| TLS_RSA_WITH_3DES_EDE_CBC_SHA (rsa 2048) – C| TLS_ECDHE_ECDSA_WITH_RC4_128_SHA (secp256r1) – C| TLS_ECDHE_RSA_WITH_RC4_128_SHA (secp256r1) – C| TLS_RSA_WITH_RC4_128_SHA (rsa 2048) – C| TLS_RSA_WITH_RC4_128_MD5 (rsa 2048) – C| compressors:| NULL| cipher preference: server| warnings:| 64-bit block cipher 3DES vulnerable to SWEET32 attack| Broken cipher RC4 is deprecated by RFC 7465| Ciphersuite uses MD5 for message integrity|_ least strength: C
To run the above-specified command, we will have first install Nmap in our machine. After installing open the command prompt and run the command on the target IP address.
Following is the POC where we can see that the target network is vulnerable to a sweet32 birthday attack
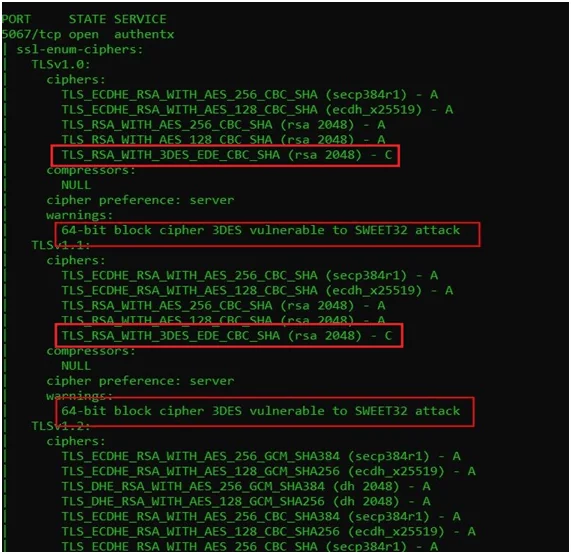
In the above POC, we can clearly see in the warning that the target is vulnerable to the sweet32 attacks.
Impact:
The consequences include:—
- Man-in-the-middle attack: A man-in-the-middle (MITM) attack can be conducted by an attacker on the communication channel to sniff data. It is possible to use such data for malicious purposes.
- Birthday attack: In probability theory, this attack exploits the birthday theory. According to the birthday theory, there might a chance of collision on the hash functions being used.
Mitigations:
Stopping the use of legacy 64-bit block ciphers is the obvious way to prevent these attacks. Alternatively, by continuously rekeying the session, the attack can be mitigated.
Specifically, the following steps are recommended to avoid our assault:
- Web servers and VPNs should be designed such that 128-bit ciphers are favored. Around 1.1 percent of Alexa’s top 100k web servers, and 0.5 percent of the top 1 million, support AES, according to our scans, but prefer to use 3DESS.
- To avoid using it with servers that support AES but prefer 3DES, web browsers should offer 3DES as a fallback-only cipher.
- The duration of TLS sessions with a 64-bit cipher should be limited by TLS libraries and applications. This could be accomplished with TLS renegotiation or, in some situations, by closing the link and beginning a new one (i.e. restricting 3DES cipher suites to HTTP/1.1 Keep-Alive, SPDY, and HTTP/2).
- OpenVPN users can change the default Blowfish cipher to AES by using, for example, the AES-128-CBC cipher in the client and server configurations. They can mitigate the attack by forcing regular rekeying with reneg-bytes 64000000 if they do not monitor the server configuration.
For more help contact us at connect@nullinfosharesystems.com or visit www.varutra.com
Thank You.
Author,
Pralekya Hirmalwar
Attack and Pentest Team
Varutra Consulting Pvt. Ltd.