PA DSS V 3.2 to SUNSET by 2022
About PA DSS Formerly known as the Payment Application Best Practices (PABP), the Payment Application Data Security Standard (PA-DSS) is a global security standard that…
Privacy Now to be a Fundamental Right in India
Electronic data protection in India is currently governed by the Indian penal code, the information Technology Act 2000 – IT Act Amendment 2008, and therefore…
How we are successfully managing & delivering the Cybersecurity Services during COVID-19 situation?
By now, we all already went through COVID pandemic’s first wave. The second wave has started hitting the world. Though this was a completely new…
Web Cache Poisoning – Through Host Header Injection
Web cache poisoning is an advanced hacking technique through which an attacker can exploit the pattern or behavior of a web cache and server. But…
Apache Struts-2 Exploited to Remote Code Execution
This blog is to describe my finding on a web-based application which is a very well-known vulnerability found on Apache Struts-2 Remote Code Execution (RCE)….
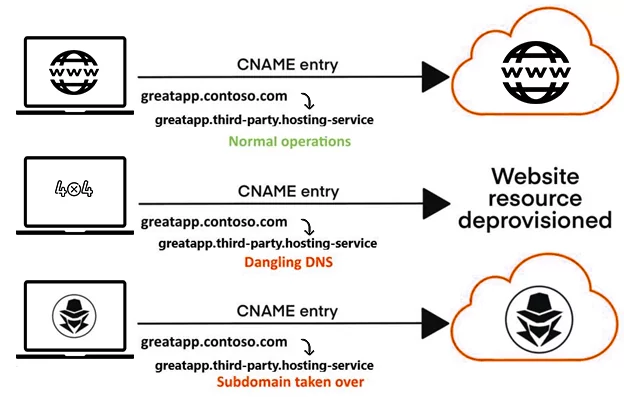
Subdomain Takeovers – CNAMEs And Cloud Services
Introduction A Subdomain Takeovers A hostile takeover of a subdomain by an attacker is known as a subdomain takeover. This issue mostly arises when organizations…
Threat Modelling – Focused Defence for Modern Enterprises
Threat modeling is creating a buzz that everyone wants to talk about it. Every organization wants to remodel its overhaul information. It will help them…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)