Security Orchestration Automation and Response (SOAR)
Cybersecurity Synopsis For almost every organization, either large or small-scale, performing incident response is an endless job and to tackle it adequately, most of the…
Android Security, Cloud Security, IOT Security, Security Best Practices
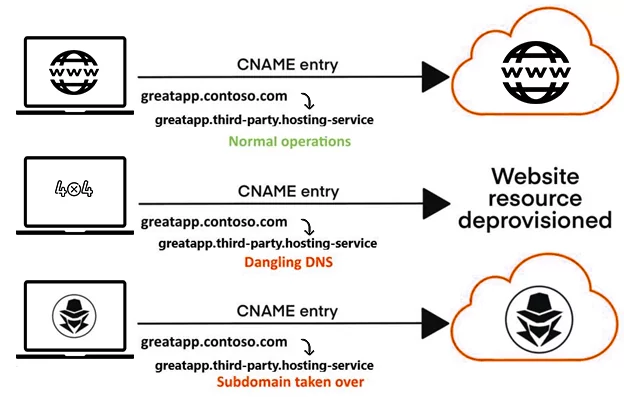
Subdomain Takeovers – CNAMEs And Cloud Services
Introduction A Subdomain Takeovers A hostile takeover of a subdomain by an attacker is known as a subdomain takeover. This issue mostly arises when organizations…
Containerization and It’s Impact on Enterprise Security
What’s this “D” word everyone is talking about? Oh.. you mean Docker!! The latest buzz word everyone is talking about and every MNC is running…
Web Services Security Testing
At present, the web services have turned into an integral portion of the both mobile and web applications. Because the many people are using the…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)