Zooming Security Vulnerabilities [Part – 2]
This blog article will cover security best practices in setting up Zoom meetings securely to avoid Zooming Security Vulnerabilities! 1. Ensure the Host can…
Zooming Security Vulnerabilities [Part – 1]
Diving into Zoom Security Vulnerabilities [Part – 1] Introduction – Zoom is a popular web-based video-conferencing application available to be installed on computer systems…
Organizations Hit by Maze Ransomware Attack !!
Introduction to Maze Ransomware – Maze ransomware is also known as ChaCha, is a ransomware that had been first discovered in the month of May…
Containerization and It’s Impact on Enterprise Security
What’s this “D” word everyone is talking about? Oh.. you mean Docker!! The latest buzz word everyone is talking about and every MNC is running…
Joanap and Brambul Malware
Joanap and Brambul Malware has come from North Korea that has infected numerous Microsoft Windows computers globally over the last decade. On 30th January 2019 United…
Best Practices – BYOD and Mobile Device Security
BYOD (Bring Your Own Device) is a practice where employees can bring their own devices such as laptops, tablets or USB drives to the workplace….
Security Advisory – Typosquatting
There are multiple cases of redirect which are due to typing mistake (typos) from the users which leads to the threat of getting infected with…
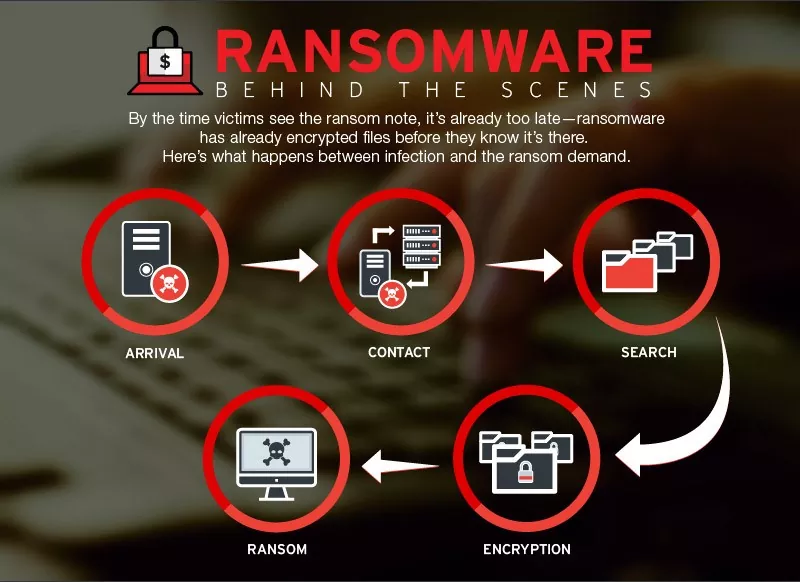
Security Advisory – Ransomware Attack Targeting China – December 2018
Ransomware Attack Targeting China – Security Advisory 1. Ransomware through Supply Chain Attack: A new ransomware strain spreading as a result of supply chain attack…
Security Advisory – Tecnimont Cyber Theft
Tecnimont Cyber Theft – Security Advisory Background: Maire Tecnimont SpA is the parent company of the Italian group Maire Tecnimont, which consists of at…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (34)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (35)
- Data Leakage (27)
- Data Privacy (29)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (42)
- Governance Risk & Compliance (8)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (48)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)