Web Services Security Testing
At present, the web services have turned into an integral portion of the both mobile and web applications. Because the many people are using the…
Introduction to Internet of Things (IoT)
Introduction to Internet of Things (IoT) and IoT Security Challenges Information security, often referred to as InfoSec, is a set of strategies to protect sensitive…
Case Study – New way to Exploit Java Deserialization Vulnerability
Introduction In this case study, we will not focus on how serialization vulnerabilities and how they work because there are plenty of articles on this…
Security Advisory- MEGA Chrome Extension Hijack
What is MEGA? MEGA is a cloud storage and file hosting service offered by Mega Limited, a New Zealand-based company. The service is offered primarily…
Advisory | Microsoft Zero Day – Windows Task Scheduler Local Privilege Escalation Vulnerability
Introduction to Microsoft Zero Day Vulnerability A previously unknown zero day vulnerability has been disclosed in the Microsoft’s Windows operating system that could help a…
Thick Client Penetration Testing – Exploiting JAVA Deserialization Vulnerability for Remote Code Execution
Thick Client? What do you mean by that? Thick client is the kind of application which is installed on the client side and major of…
What Makes Penetration Testing Impactful – Post Exploitation
As a penetration tester, we often come across this riddle – What Makes Penetration Testing Really Impactful. As per penetration testing methodology – we identify…
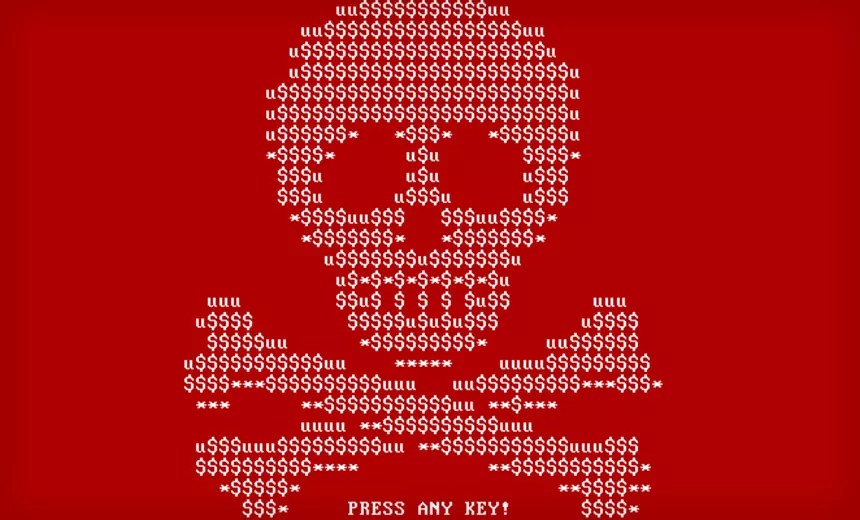
Threat Advisory Report on Petya Ransomware (Critical Severity)
Threat Advisory Report on Petya Ransomware Attack (Critical Severity) Ransomware: An Introduction Ransomware is a form of malicious software that locks up users files on…
Beware Android Users – CLOAK AND DAGGER is here to exploit you
The WORLD has still not got over with the WannaCry ransomware menace and here comes one more android ransomware – Cloak and Dagger! People have…
Buffer Overflow Attacks
Introduction to Buffer Overflow Buffer is a storage place in memory where data can be stored. It’s mostly bound in a conditional statements to check…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (34)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (35)
- Data Leakage (27)
- Data Privacy (29)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (42)
- Governance Risk & Compliance (8)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (48)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)