Importance of Biometrics in Cybersecurity
Introduction Cybersecurity refers to safeguarding the systems, networks, and applications against digital attacks intended to gain access to, alter, or delete sensitive data, extort money…
Code Injection Vulnerabilities
Introduction to Code Injection Vulnerabilities Code injection is an attack where the attacker tries to inject a code that can be interpreted and executed by…
Dark Web Ads Offering Access to Corporate Networks
The rate of cybercrime increased in the first half of 2020 due to the pandemic. The total volume of cyber attacks increased by 35% when…
AWS Pentesting – Part – 1
Nowadays, we have experienced many data breaches exposing different vulnerabilities like s3 buckets, compromised AWS cloud environments, and many more so avoid this it is…
Organizations Hit by Maze Ransomware Attack !!
Introduction to Maze Ransomware – Maze ransomware is also known as ChaCha, is a ransomware that had been first discovered in the month of May…
Formjacking – The New Favourite Cyber Crooks Hack
“We are in the most popular world of – Black hat hacker” What is Formjacking Attack? The year’s rampant threat in cybersecurity is Formjacking attack….
Security Advisory – Ransomware Attack Targeting China – December 2018
Ransomware Attack Targeting China – Security Advisory 1. Ransomware through Supply Chain Attack: A new ransomware strain spreading as a result of supply chain attack…
Security Advisory – Tecnimont Cyber Theft
Tecnimont Cyber Theft – Security Advisory Background: Maire Tecnimont SpA is the parent company of the Italian group Maire Tecnimont, which consists of at…
Security Advisory – Saipem Cyber Attack by Shamoon Malware
Saipem Cyber Attack by Shamoon Malware 1. Introduction Saipem identified cyber-attack on Monday i.e. on 10th December 2018 that had primarily affected its servers in…
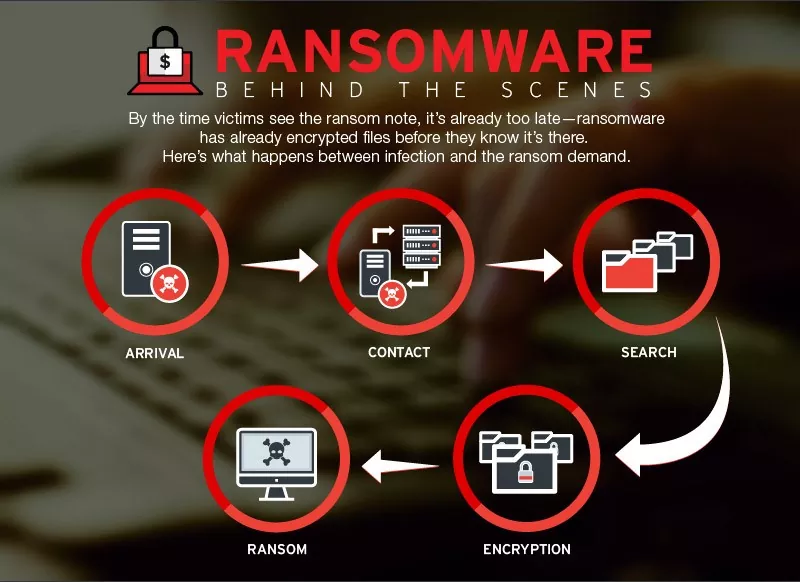
Threat Advisory Report on Petya Ransomware (Critical Severity)
Threat Advisory Report on Petya Ransomware Attack (Critical Severity) Ransomware: An Introduction Ransomware is a form of malicious software that locks up users files on…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (34)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (35)
- Data Leakage (27)
- Data Privacy (29)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (42)
- Governance Risk & Compliance (8)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (48)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)