What to Expect When You’ve Been Hit with Ransomware?
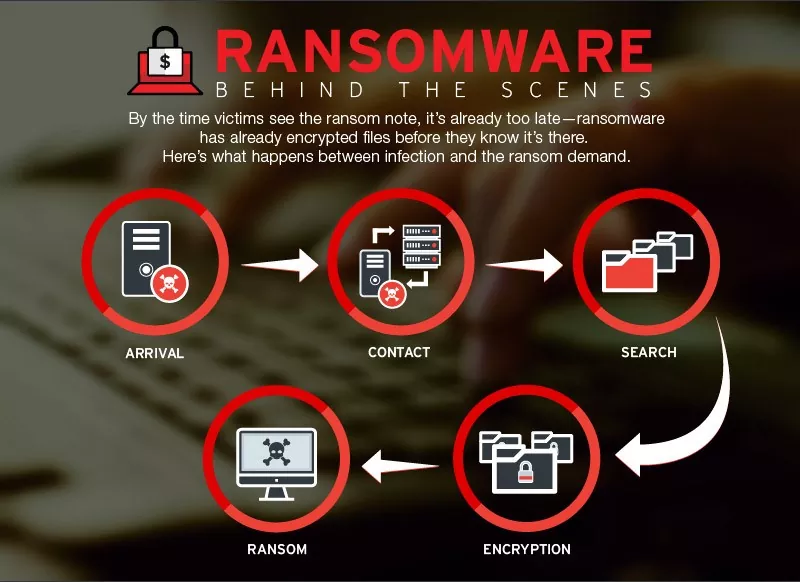
Ransomware is malicious software or malware that gains access to the system, denies you any admission to your network, system, or files, and demands payment…
Cyber Attack, Data Breaches, Email Phishing, Encryption & Cryptography, Ransomware Attack, Security Best Practices
Top 10 Cybersecurity Threats
There is a significant shift in the digital landscape as people rely on the internet more and more across the globe. But unfortunately, it also…
Ransomware and the measures to safeguard an organisation
Ransomware Attack and Its Prevention We are all aware of ransomware, as most of us, or at least someone in our connection might be a…
Security Advisory – Ransomware Attack Targeting China – December 2018
Ransomware Attack Targeting China – Security Advisory 1. Ransomware through Supply Chain Attack: A new ransomware strain spreading as a result of supply chain attack…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)