Vulnerabilities Related to SAML [Security Assertion Markup Language] – Part 1
In this blog, we are going to discuss about what is the SAML (Security Assertion Markup Language) and how it works as well as we…
Security Advisory – Typosquatting
There are multiple cases of redirect which are due to typing mistake (typos) from the users which leads to the threat of getting infected with…
Best Practices to Harden Office 365
Here are some best practices to harden office 365 and ensure your data remains protected. 1. Password Policy It is always recommended to use a…
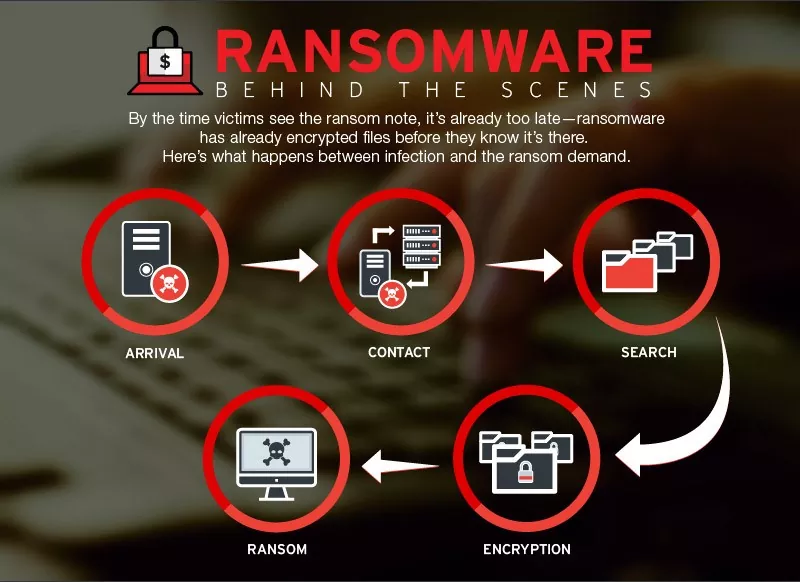
Security Advisory – Ransomware Attack Targeting China – December 2018
Ransomware Attack Targeting China – Security Advisory 1. Ransomware through Supply Chain Attack: A new ransomware strain spreading as a result of supply chain attack…
Security Advisory – Tecnimont Cyber Theft
Tecnimont Cyber Theft – Security Advisory Background: Maire Tecnimont SpA is the parent company of the Italian group Maire Tecnimont, which consists of at…
Security Advisory – Saipem Cyber Attack by Shamoon Malware
Saipem Cyber Attack by Shamoon Malware 1. Introduction Saipem identified cyber-attack on Monday i.e. on 10th December 2018 that had primarily affected its servers in…
Microsoft Zero Day – VCard Vulnerability
In this blog we are going to discuss about Microsoft Zero Day – VCard Vulnerability For Windows operating system. Introduction Microsoft Zero Day – VCard…
The Art of Communication, Interpretation & Validation: ChatBots
“Hello Alexa, may I have a strategy to test you? “ What is ChatBot? A computer program designed to simulate conversation with human users…
Blockchain Security – Part 1
Blockchain is both a strength and a concern. Know basics of blockchain and blockchain security security practices to make it as secure as possible. Blockchain…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (33)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (34)
- Data Leakage (27)
- Data Privacy (28)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (41)
- Governance Risk & Compliance (7)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (47)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)