Security Advisory – Saipem Cyber Attack by Shamoon Malware
Saipem Cyber Attack by Shamoon Malware 1. Introduction Saipem identified cyber-attack on Monday i.e. on 10th December 2018 that had primarily affected its servers in…
The Art of Communication, Interpretation & Validation: ChatBots
“Hello Alexa, may I have a strategy to test you? “ What is ChatBot? A computer program designed to simulate conversation with human users…
Blockchain Security – Part 1
Blockchain is both a strength and a concern. Know basics of blockchain and blockchain security security practices to make it as secure as possible. Blockchain…
Security Advisory- MEGA Chrome Extension Hijack
What is MEGA? MEGA is a cloud storage and file hosting service offered by Mega Limited, a New Zealand-based company. The service is offered primarily…
Advisory | Microsoft Zero Day – Windows Task Scheduler Local Privilege Escalation Vulnerability
Introduction to Microsoft Zero Day Vulnerability A previously unknown zero day vulnerability has been disclosed in the Microsoft’s Windows operating system that could help a…
Thick Client Penetration Testing – Exploiting JAVA Deserialization Vulnerability for Remote Code Execution
Thick Client? What do you mean by that? Thick client is the kind of application which is installed on the client side and major of…
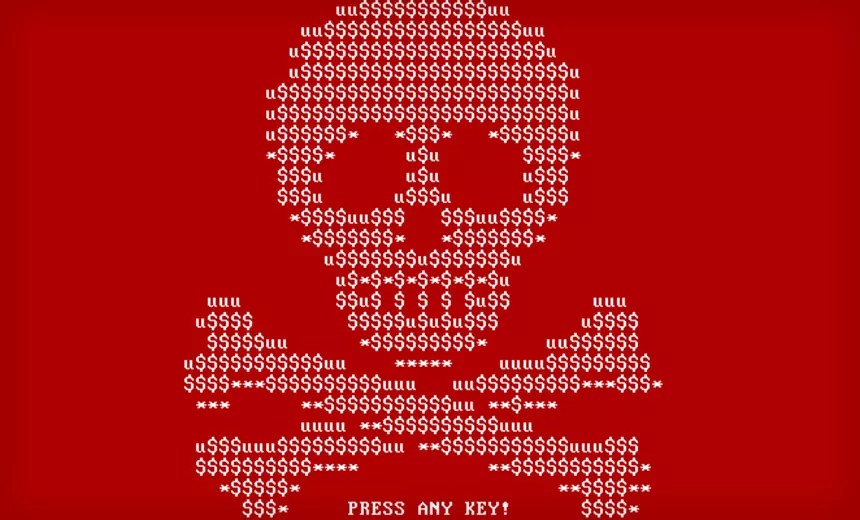
Threat Advisory Report on Petya Ransomware (Critical Severity)
Threat Advisory Report on Petya Ransomware Attack (Critical Severity) Ransomware: An Introduction Ransomware is a form of malicious software that locks up users files on…
Threat Advisory Report on WannaCry Ransomware (Critical Severity)
Here we will discuss Threat Advisory Report on WannaCry Ransomware (Critical Severity). 1. Introduction On Friday, May 12, countless organizations around the world began fending…
Adobe Flash Player Zero Day Attacks Found In Hacking Team Data Leaked
Hacking Team is a Milan-based information technology company that sells offensive intrusion and surveillance capabilities to governments, law enforcement agencies and corporations.Its “Remote Control Systems”…
CSRF Vulnerability on LinkedIn
In previous blog we have seen a critical vulnerability in LinkedIn password reset module allowing an attackers to compromise LinkedIn user’s account and how helpless…
Categories
- Android Security (19)
- Application security (1)
- Authentication & Authorization (23)
- Blockchain Security (1)
- Bug Bounty (2)
- BYOD (5)
- Case Study (29)
- Chatbot Security (1)
- Cloud Security (14)
- Containerization Security (1)
- Corporate Training (6)
- Cyber Attack (34)
- Cybersecurity Frameworks and Solutions (3)
- Data Breaches (35)
- Data Leakage (27)
- Data Privacy (29)
- Email Phishing (8)
- Encryption & Cryptography (14)
- Ethical Hacking (19)
- General (42)
- Governance Risk & Compliance (8)
- iOS Security (2)
- IOT Security (7)
- Java Security (2)
- Mobile Application Security (19)
- Mobile Device Management (10)
- Network Pentesting (9)
- News (48)
- Password Security (10)
- Past Events (8)
- Patch Management (3)
- Ransomware Attack (14)
- Reverse Engineering (3)
- Secure SDLC (5)
- Security Advisory (34)
- Security Best Practices (43)
- Security Hardening (38)
- Social Engineering Attack (10)
- Social Networking Security (5)
- Source Code Review (2)
- SPAM (2)
- Student Oriented Courses (2)
- Thick Client Penetration Testing (4)
- Unix/Linux Security (1)
- Upcoming Events (3)
- Viruses & Malware (16)
- VoIP Penetration Testing (4)
- Vulnerability Disclosure (21)
- Web Application Security (34)
- Windows Mobile Security (1)
- Zero Day Attack (8)